How to Add Identity Context to RADIUS Auth for ZTNA
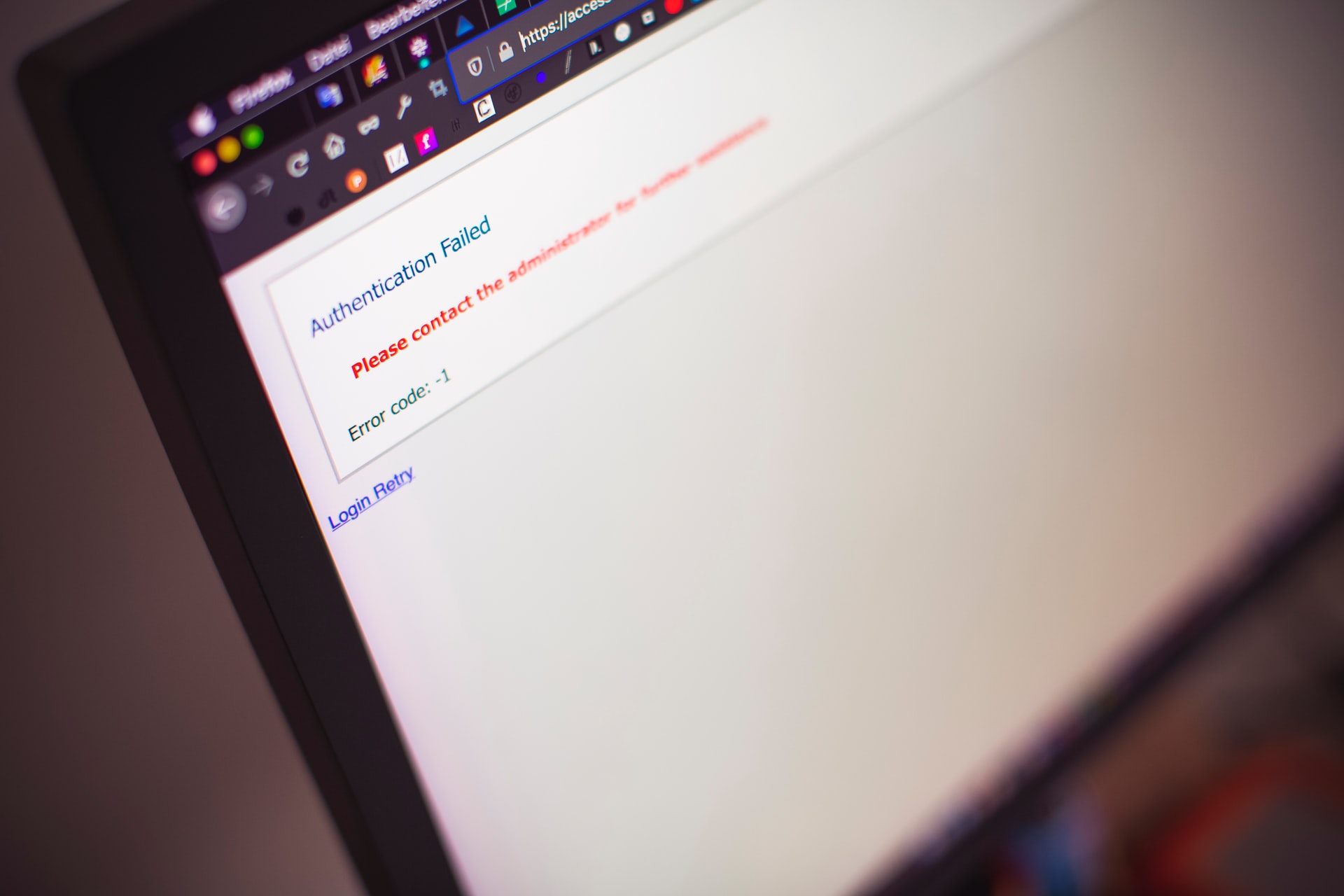
Impersonating machines in the digital age is becoming very convenient. Hackers constantly employ these techniques to penetrate the defenses of business networks. Once inside their trusted gadgets, they can travel laterally across systems to steal encrypted data. Here’s a recent cyberattack reported by the Department of the Treasury’s Office of Foreign Assets Control (OFAC), sanctioning […]
Read Story