Cloud-Based RADIUS Server with Azure Integration
Your Identity Provider (IDP) is a core component of any Zero Trust Network Architecture. It gives administrators the tools they need to define and segment both users and devices, so administrators spend a lot of time carefully crafting policies based on these groups.
One of the most popular IDPs today – used by an estimated 95% of Fortune 500 companies – is Azure Active Directory (commonly called Azure AD). However, the policies you create in Azure don’t just need to end there – with all the work you’ve put into them, you may be interested to learn that you can easily extend these policies to your network including your Wi-Fi through the use of RADIUS security.
In fact, the right cloud-based RADIUS server can integrate with your Azure and leverage all the policies you’ve already created for authentication across all of your apps and services, including desktop login, Wi-Fi, VPN, SSO, and more. We’ll explain how it works.
Does Azure AD Have RADIUS?
Azure does not have a RADIUS itself, but Microsoft does have its own optional RADIUS server called the Network Policy Server (NPS). NPS is commonly used alongside Microsoft Active Directory in organizations striving to achieve 802.1X.
In a Microsoft-heavy environment, NPS may be the first RADIUS solution that comes to mind. However, there are many drawbacks to also keep in mind before deploying it within your own organization.
First, NPS is tied to on-premise infrastructure, along with Microsoft Active Directory. On-premise infrastructure is generally costlier than the cloud, especially if you take the time to do it correctly. What’s more, the cost tends to increase exponentially as you replicate it across multiple locations.
NPS can also be difficult to set up if you don’t already have experience working with RADIUS servers. This means that deployment will take time and potentially even more in cost if you need to bring on security specialists with experience.
If you, like many other organizations, are migrating to the cloud with cloud-based IDPs like Azure, then you’ll want a cloud-based RADIUS service to match.
Cloud RADIUS vs NPS
Many organizations with Microsoft-heavy environments are tempted to just use NPS instead of investing in anything else. While you theoretically can just use NPS for your RADIUS security, there are a few hurdles you’ll need to overcome along the way – as we discussed above.
However, there are still other hurdles to consider. For instance, NPS only supports PEAP, an authentication protocol that uses credentials. With hacking methods growing increasingly sophisticated, passwords simply aren’t as secure an option anymore.
NPS is generally tied to on-premise infrastructure. If you intend to use it with cloud components, you’re going to need its cloud extension – which will require you to have a cloud RADIUS proxy, anyway. If you’re going to have a cloud-based proxy RADIUS, why not just invest in a cloud RADIUS server from the get-go and save yourself an additional step?
Finally, NPS does not currently support advanced RADIUS features, including Change of Authorization or Identity Lookup. Updates are integral to keeping up with emerging cybersecurity threats.
These hurdles aren’t present when it comes to Cloud RADIUS. Because it’s cloud-based, it can scale across all your locations and you won’t need to hire a team of experts to deploy it. Moreover, Cloud RADIUS’s built-in vendor neutrality means it can integrate with your infrastructure beyond just your IDP. This isn’t the case for NPS, which tends to integrate best when used with other Microsoft products.
Integrating Cloud RADIUS with Azure AD
Cloud RADIUS was created to be vendor-neutral. It can integrate with your infrastructure easily, and many of our customers have found it works perfectly with Azure. This is because it has plenty of features that allow it to integrate with Azure, including:
- Passwordless Authentication
- Identity Lookup
- Azure Policy Application
Passwordless Authentication
Passwords unnecessarily expose your network to a number of threats. Examples of attacks that target passwords include:
- OTA and MITM attacks
- Phishing
- Brute Force attacks
…just to name a few. With that in mind, it’s easy to see why protecting your Wi-Fi and VPN with a password is becoming an increasingly less tenable practice, especially since poor password management can be a reason for cybersecurity insurance to deny coverage.
The beauty of Cloud RADIUS is that it was designed from the ground up for passwordless authentication through digital certificates. It combines with a PKI for a seamless authentication experience. If you don’t have a PKI already, our solution can come with a managed PKI to create as many certificates and certificate authorities as you need, as well as self-service onboarding for unmanaged devices and auto-enrollment for managed devices.
These certificates can be distributed using the policies you’ve already created in Azure. For instance, certificates can be issued by different certificate authorities (CAs) based on the department a user is in. You can even use these certificates to log into Azure applications, thanks to Azure AD certificate-based authentication (CBA).
Identity Lookup
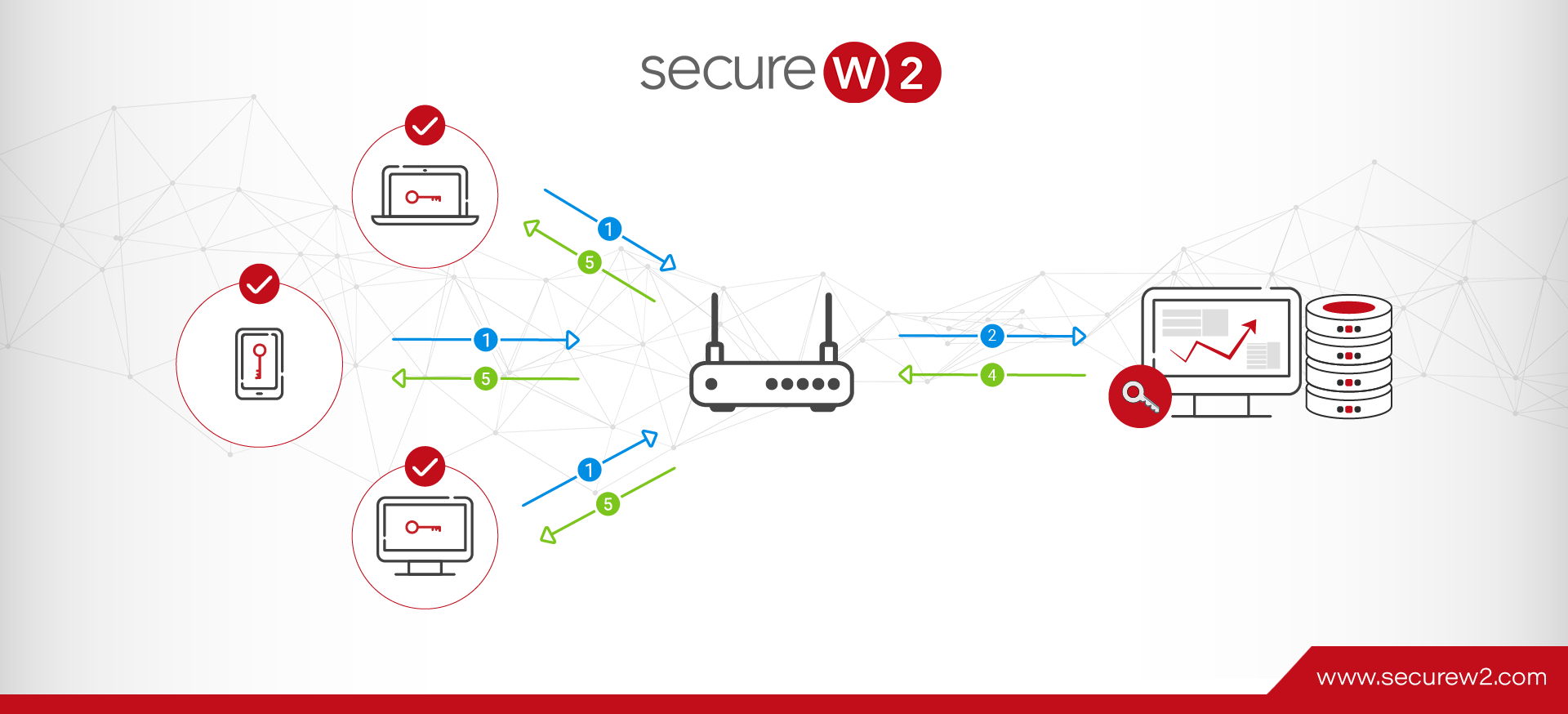
Typically, a RADIUS server follows these steps when it goes through the authentication process:
- The device attempts to connect to your network and presents a certificate to the RADIUS server.
- The RADIUS checks that the device’s certificate is unexpired.
- If the certificate is unexpired, the RADIUS then checks to see if the certificate is on the Certificate Revocation List (CRL) to confirm whether or not it has been revoked.
However, with Identity Lookup, a feature Cloud RADIUS has, there’s an additional step: checking your directory in real-time by searching with the information in the certificate’s template.
The reason this matters is that it allows for the most up-to-date application of policies to any user and device as they authenticate to the RADIUS. Administrators can update said policies within Azure itself, then when the RADIUS cross-checks a user in the directory during the Identity Lookup phase, the RADIUS can use the policy updates that were added.
Azure Policy Application
You put a lot of effort into carefully developing policies in Azure. Similarly, you spend a lot of time creating organized groups for different employees to apply policies to.
These groups and policies are vital to the concept of Zero Trust, which asserts that users continuously authenticate themselves and only have access to resources they absolutely need. But your policies shouldn’t just be limited to Azure and its applications – and they don’t have to be.
With Cloud RADIUS and our managed PKI service, you can extend your Azure policies to both your Wi-Fi and VPN. As we mentioned above, Cloud RADIUS can communicate directly with your IDP and apply relevant policies as users authenticate to your network. One common example of this is the ability to designate different devices to different VLANs based on the groups they belong to.
Deploy a Cloud RADIUS Solution that Natively Integrates with Azure AD
RADIUS authentication doesn’t need to be complicated to set up, nor does its deployment need to be lengthy. Cloud RADIUS, backed by a team of knowledgeable engineers, was created to smoothly integrate with your existing infrastructure and deploy rapidly.
Combined with the security of digital certificates, Cloud RADIUS empowers administrators to leverage their existing Azure policies for Wi-Fi and VPN authentication. All this is simple, efficient, and economical – see for yourself how one of our customers used Cloud RADIUS and Azure AD to secure their Wi-Fi.
Amanda Tucker
Amanda Tucker covers network security at SecureW2, where she has spent 5 years writing about PKI, RADIUS authentication, 802.1X, continuous trust, and device onboarding. She translates complex certificate and authentication concepts into practical guidance for IT and security teams. Amanda brings 7 years of professional writing experience and a background in research and analysis.