How FreeRADIUS Supports MAC Auth Bypass for IoT Security
While IoT devices are embedded into our daily lives, they can be hard to protect. They use non-standard operating systems, like real-time operating systems (RTOS) that lack built-in security features and cannot always handle the 802.1x protocol. This is where MAC Authentication Bypass (MAB) comes into the picture.
MAB checks the unique MAC address of the device connected to the network instead of standard login credentials. If the device is verified as trusted, the network switch or controller gives access to it in the given network. FreeRADIUS, an open RADIUS server, plays a vital role in the authentication of IoT devices incapable of advanced authentication methods like 802.1x.
What is Remote Authentication Dial-In User Service (RADIUS) MAB
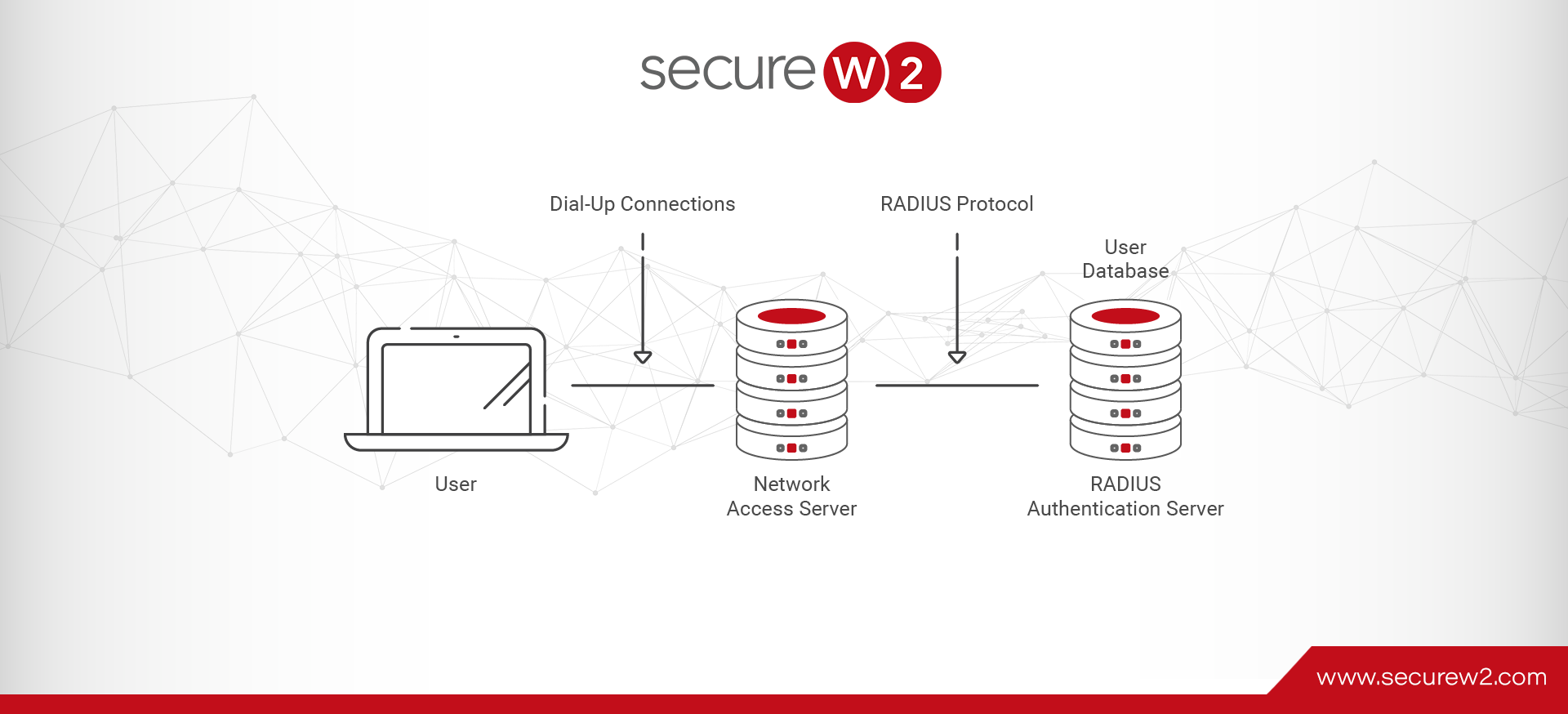
A Remote Authentication Dial-In User Service (RADIUS) server is a centralized server that determines whether a user or machine trying to connect to a network is authorized to access it and what level of access they are to be provided.
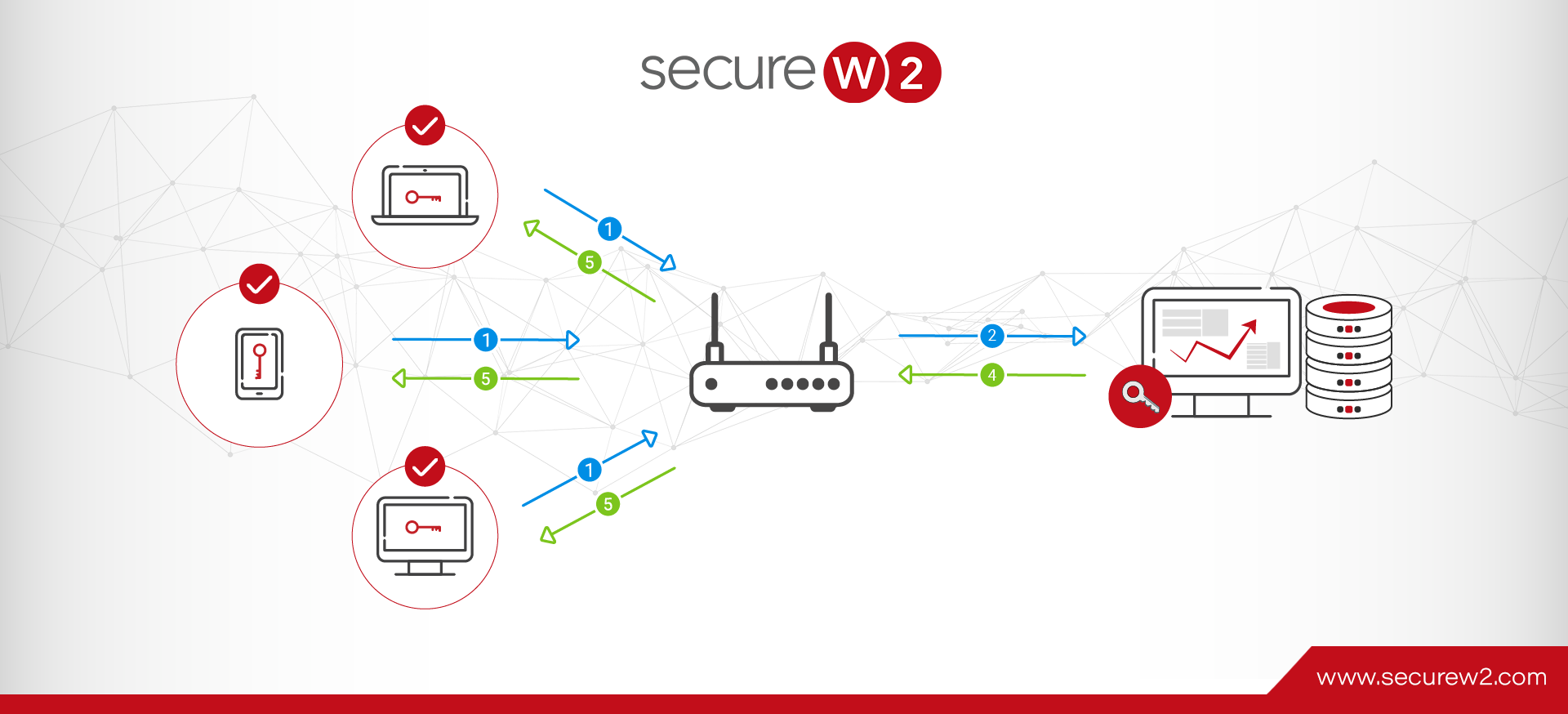
A Cloud RADIUS verifies the login credentials or certificates for machines that are on the 802.1X network. The access level granted to the user, or machine, is determined by a lookup carried out by RADIUS with Identity Providers (IDP) like Entra ID, Google, or Okta.
A MAB must be enabled to authenticate IoT devices through RADIUS. MAB can identify, authenticate, and determine the level of access of a device for IoT devices that do not support 802.1X configuration. When MAB is used with a RADIUS server, it’s called RADIUS MAC Authentication Bypass. RADIUS MAB can help minimize threats l and make IoT devices visible and easier to monitor and control.
MAB to Secure IoT Devices
MAB is a solution that can improve the security of IoT devices and help you manage their network access. Let‘s examine how it works.
MAB
MAB is an alternative protocol for authenticating devices that don’t support 802.1X. In this protocol, a machine’s MAC address is used as the unique identifier to authenticate a device before allowing it access to a network. Though MAB is not the most secure network authentication method, visibility and entity-based access control help bring otherwise unmanaged IoT devices under your network security purview.
Access management can be managed dynamically with MAB. Users’ activity can be monitored, and access can be revoked in real-time if any threat is detected. Since MAB is port-based, it allows a company to limit the devices’ network access to only the degree that they need to function. MAB can work basically in two modes:
● Multi-authentication host mode:
In multi-host mode, multiple devices can authenticate on a single port automatically after a single device is authorized.
● Single host mode
In single-host mode, only one device can be authenticated on a single port at a time, and no other devices can be authenticated while one is already authenticated.
MAB uses MAC address filtering to check if a particular MAC address has access to the network and what level of access the device is allowed.
How RADIUS MAB is Used to Authenticate Devices
Below are the steps that MAB takes to authenticate a user/machine before granting access to a network.
1. Initiation
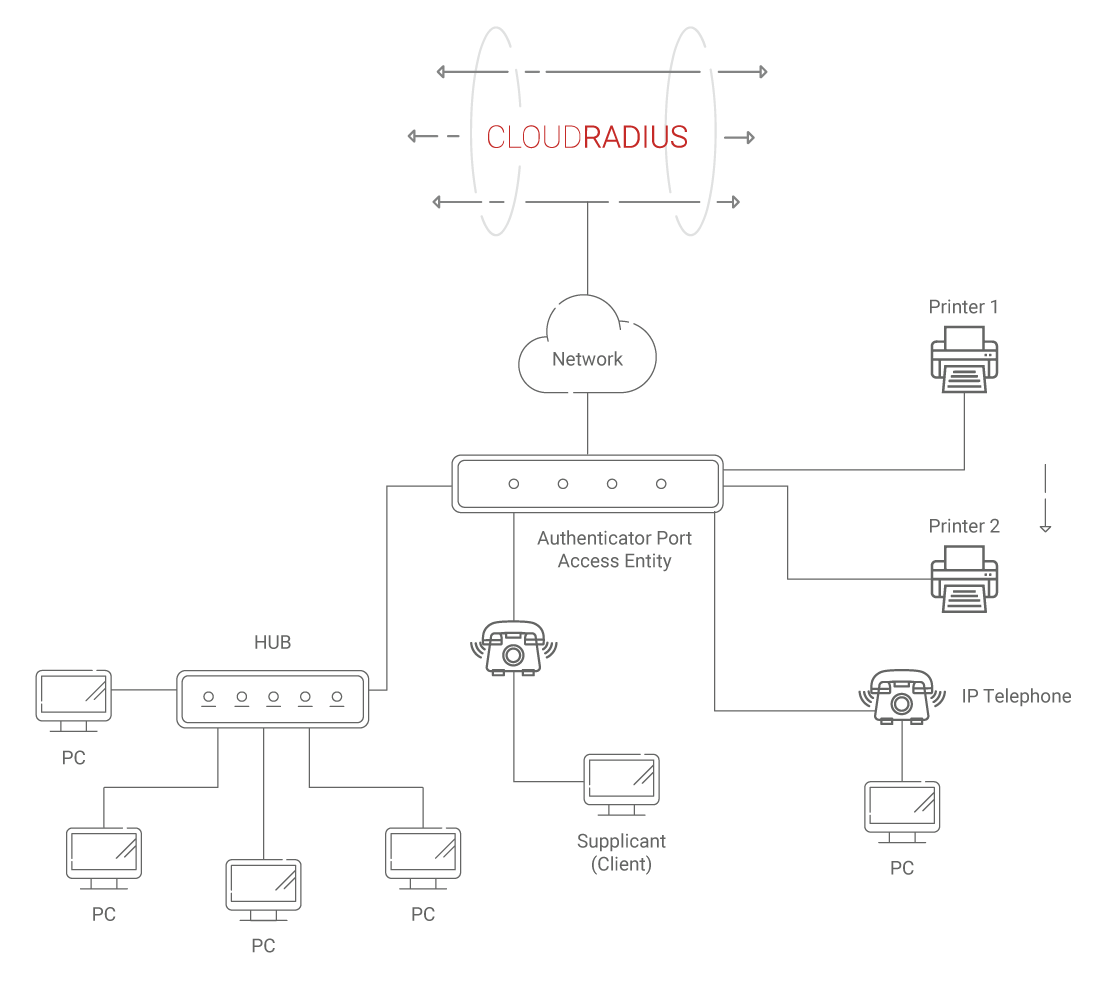
RADIUS is not involved in the first step since it is done at the switch. When the switch identifies that a device is trying to connect to the network, it submits an EAPoL identity request three times at 30-second intervals to the endpoint. If the endpoint does not respond after the third attempt, the switch concludes that the endpoint lacks an 802.1X supplicant and attempts to use MAB to authenticate the device.
2. RADIUS Mac Authentication
Once the switch determines that a device does not have a supplicant, it then initiates MAB. First, the switch accepts a single packet from an interface to determine the origin of the endpoint’s MAC address. After identifying the source MAC address, the packet is discarded, and a RADIUS access-request message is created with the device’s MAC address as the identity. This access-request message is then sent to the RADIUS server so that it may perform MAC authentication.
3. Authorization
The last step is where the RADIUS authentication server decides if the machine requesting access can be granted entry to the network using the network profile and the level of access to the network the client/machine is to be given. Authorization options like Downloadable ACLs (dACLs), Dynamic VLANs (dVLANs), configuration profiles, and Security Group Tags (SGT) are applied by RADIUS to determine, create, and transmit access-accept to grant the user/machine access to the network.
FreeRADIUS & MAB
MAB can be used with FreeRADIUS to authenticate machines that do not support 802.1X. There are multiple ways to use MAB in FreeRADIUS. Some of the modes are as follows.
1. MAB as a Stand-Alone Protocol
This is the protocol where FreeRADIUS does MAB directly or as the only protocol for authentication. In this method, the machine’s MAC address is enough to authenticate before granting access to the network.
2. MAB & 802.1X Alternatively
This protocol uses MAB and 802.1X alternatively, meaning either can be applied at the time of authentication. In this mode, either the MAC address or valid login credentials can be used to log in to the network. The user can access the network using either of the options.
3. MAB & 802.1X as a Combination
In this method, both MAB and 802.1X protocols are used to authenticate a device before granting access. A MAC address is used to identify a user if a machine cannot authenticate using the 802.1X protocol. When the 802.1X protocol is used, the MAC address and digital credentials are required before accessing the network.
4. Web Auth & MAC Auth
This method allows you to authenticate a machine using both web auth and MAC auth protocol. Web auth uses a web page login to authenticate users trying to access the network. After connecting to the switch, when a user opens a web page, the switch directs the user to a login page. Once the user enters the requested login credentials, the switch forwards the request to the RADIUS server that authenticates the machine and allows access to the network.
FreeRADIUS supports a number of MAB options for you to authenticate your IoT devices without 802.1X. However, misconfiguring MAB is very possible and can have dire consequences. That’s broadly true of RADIUS as well, which is why you might consider a managed RADIUS service if you don’t already have experience setting up and running a FreeRADIUS installation.
Cloud MAB with Dynamic RADIUS
MAB is not the most secure authentication protocol. However, it is an effective way to improve visibility. When MAB is used with a dynamic RADIUS that supports cloud identity lookup, it can be implemented similarly to the 802.1X network, with both VLAN assignments and a dynamic access list.
SecureW2 dynamic RADIUS is deployed in a cloud environment. It can be integrated directly into your existing PKI infrastructure for identity lookup. It also can improve your certificate-based authentication runtime-level policy enforcement and reinforce security through directory checks via a lightweight API designed to reduce request size and optimize authentication speed.
In a typical certificate-based RADIUS authentication process, the RADIUS server references the certificate revocation list(CRL) to verify if a certificate is. However, a dynamic RADIUS will directly look up the directory to verify if a user is current and to make decisions on the user privileges. When MAB is implemented with a dynamic RADIUS, you can trace network activity on these devices and limit network access with a dynamic access list in real-time.
SecureW2’s Cloud RADIUS with MAB and MAC address filtering helps you better control your IoT devices that do not support the 802.1X authentication protocol. By managing and accounting for them with MAB and MAC address Filtering, you can extend your network visibility to these unmanaged devices. Talk to our industry experts about how our solutions can help secure your IoT devices.