Dynamic VLAN Assignment for Cloud RADIUS
The landscape of cybersecurity is always changing, but there are a few constants. One unchanging aspect is the use of VLANs as a primary method of segmenting users and network resources. Like the Local Area Network it emulates, a VLAN is a useful tool for isolating sensitive resources and sheltering it from risk created by unnecessary access.
Our networks are becoming increasingly virtual, as illustrated by the industry trend of moving to the cloud. That makes VLAN more important than ever and, fortunately, VLAN technology is keeping pace. In this article we will discuss the methods through which users are assigned to VLANs and how to automate the process for ease-of-use and increased security.
What is Dynamic VLAN Assignment?
Dynamic VLAN Assignment, also referred to as “VLAN Steering”, is exactly what it sounds like. The process of assigning users or groups of users to VLAN can be handled by a RADIUS at the time of authentication, though the infrastructure and expertise needed for dynamic VLAN assignment has historically been an obstacle for smaller organizations.
Why use Dynamic VLAN Assignment?
The default state of a wireless (or wired) network is sometimes described as “flat”. Every user in the organization is tossed into a shared network that also contains all of the resources that organization has (files, data, source code, applications, etc.). Everyone potentially has access to everything, even if there is another login portal between them and, say, the payroll system.
That’s an unnecessary risk. Developers need access to very sensitive resources like the source code for their app, but that doesn’t imply that they require access to everything that is less confidential. It’s a basic tenet of security, cyber or not, to restrict access to only people that require it.
Those are the guiding principles that lead us to implement VLANs, but the “dynamic assignment” portion of dynamic VLAN assignment is equally important. There needs to be an automated process by which users are automatically shunted to the appropriate VLAN. Relying on IT to manually assign VLANs is short-sighted – humans are fallible and it doesn’t scale past a couple dozen users.
RADIUS Attributes for Dynamic VLAN Assignment
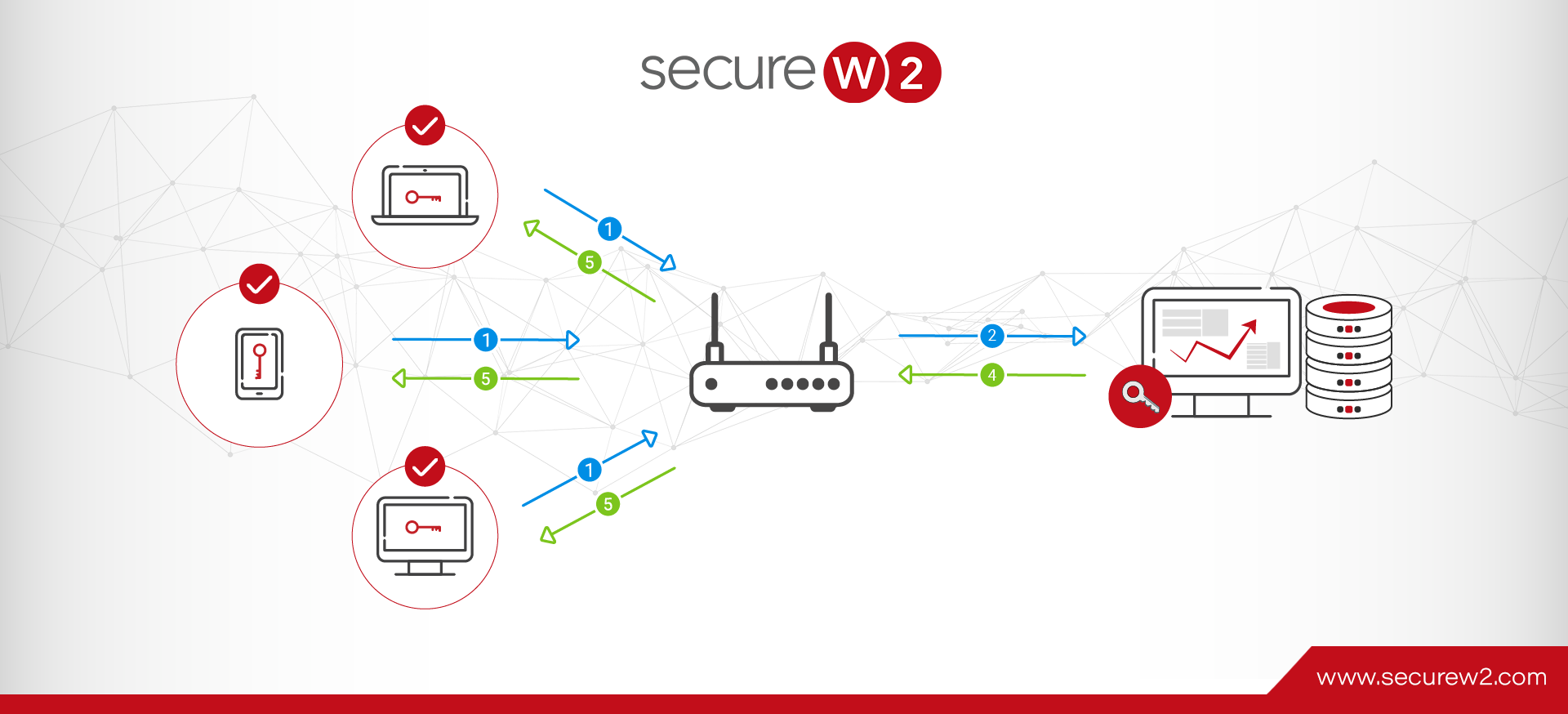
That’s why we configure a RADIUS server to assign users for us. It already has the responsibility of authorizing and authenticating users for network access, so it’s a relatively simple task to configure it to send users to a switch that can further sort users to a specific access point and/or a specific VLAN.
How does a RADIUS decide where to send the user? By the attributes assigned to them. Attributes are often stored as part of the user profile in the directory or as a part of the device/client profile for MAC authentication. SecureW2’s Cloud PKI can even amend attributes to digital certificates for seamless certificate-based EAP-TLS authentication with dynamic VLAN assignment.
The majority of VLAN assignment is done by configuring these 3 attributes:
- Tunnel-Type
- Tunnel-Medium-Type
- Tunnel-Private-Group-ID
SecureW2’s Cloud RADIUS supports additional VLAN assignment attributes such as:
- NAS-ID
- SSID
- MAC
- Custom groups
These additional parameters allow you an even greater degree of control and flexibility in assigning users to VLANs so that you can efficiently maximize your network security.
Which RADIUS for Dynamic VLAN Assignment?
Most, though not all, RADIUS servers can be configured to support dynamic VLAN assignment. Keep in mind the other needs of your organization when choosing which to configure.
Microsoft’s NPS is a popular DIY RADIUS solution because many organizations are already using a Microsoft environment. The ubiquitous Active Directory remains one of the most popular identity providers even though it’s mostly incompatible with many cloud-based applications and services (including Microsoft’s own Azure AD). The lack of compatibility with cloud services more or less eliminates NPS as a choice.
FreeRADIUS is another DIY RADIUS which actually is able to interact with cloud directories and the like. Unfortunately, the lack of a GUI is a turn off for most enterprises that want deep customizability and reporting.
SecureW2’s Cloud RADIUS is equipped with the latest in VLAN technology. Our Dynamic Policy Engine enables the RADIUS to make runtime-level policy decisions by directly referencing user attributes stored in any directory (including cloud directories like Google, Azure, and Okta). Not only does this reinforce the network segmentation of VLAN, but it also enables passwordless authentication for any cloud directory via the use of digital certificates.
If your organization already has an 802.1X network, SecureW2’s turnkey solutions can integrate into your network without any forklift upgrades. If you’re still considering the transition to a secure WPA2-Enterprise network, you’ll be interested in our managed Cloud PKI which has all the components necessary for top-of-the-line X.509 digital certificate security right out of the box.
We have affordable options for organizations of all sizes. See our pricing here.