Do Passwords Diminish UX In RADIUS?
Most companies have moved to remote work or hybrid work models, changing the scope of cybersecurity dramatically. With users logging in using their own private Wi-Fi or VPN connections (sometimes on public or shared ones), the use of RADIUS protocol to authenticate users keeps your networks secure and prevents any unauthorized access by providing powerful cryptography.
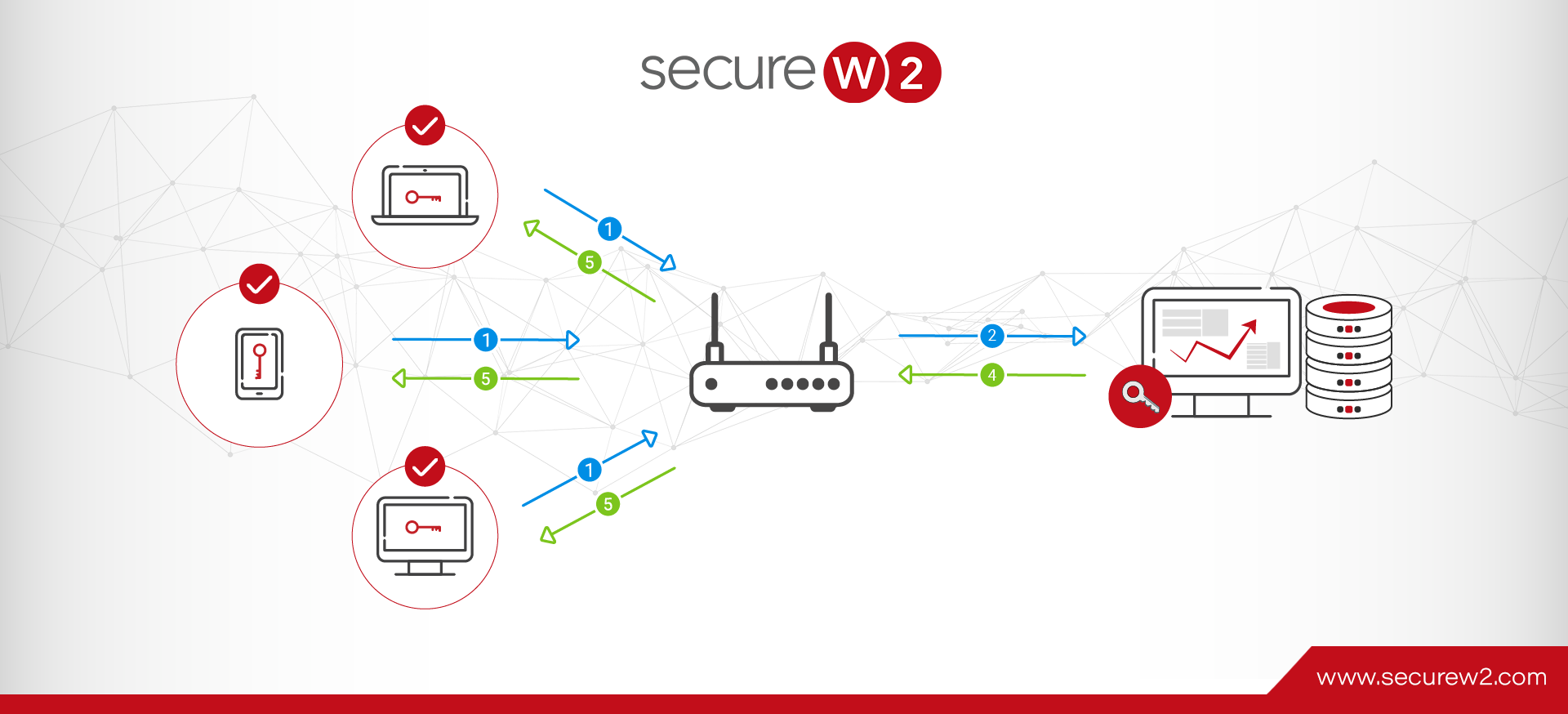
RADIUS servers to authenticate user identity is one of the vital components of the 802.1x network, the gold standard for network security. RADIUS server authentication ensures that only the right user has access to the information.
In this article, we will explore the use of password (EAP-TTLS PAP) and passwordless (EAP-TLS) authentication protocols in RADIUS servers and user experiences for each of them. Also, we will discuss why passwordless authentication protocol provides a better user experience using a story that hopefully will make the concept more relatable.
Credential Based RADIUS Authentication User Experience
Simon recently joined an ad agency as a digital marketing specialist where he was creating a pitch for an ad for a prestigious beauty products company. Once he joined, his agency’s IT support team provided him with all the necessary usernames and passwords including the passphrase needed to log in to their network. His company used the EAP-TTLS/PAP protocol to authenticate users logging in to their network.
Simon wrote down all his passwords on his phone to ensure he had them handy. Excited with the prospect of making his mark, Simon started brainstorming ideas to make a unique pitch to impress the company.
End of the first week, his boss took the team out for a party. At around 3 in the morning when they finally decided to wrap up the party, Simon realized that his phone was missing. He started panicking since his phone had all his office account passwords and there was nothing he could do but wait till 9 in the morning before he could call his IT support team.
He managed to get hold of the IT desk first thing in the morning and got a new password reset to log in to his system and since his other login details were already stored on his system, he didn’t bother requesting to change them. In the rush of getting his presentation completed, Simon started working on it immediately and finally managed to get everything ready to present the pitch to their client. The client was impressed and asked to get the final version ready for the campaign.
The next morning, on his way to the office Simon was shocked to see collections of new ads for their client’s competitors with his exact idea. The rest we all know is history.
His IT team later discovered that someone accessed their network multiple times. Since the password to connect to the network remained the same no one suspected any foul play till it was too late.
EAP-TTLS/PAP User Experience
Simon’s story, though it might sound like a cliche, is relatable to most of us who use passwords to log in to work servers. No matter how robust your organization’s password protocols are, there is always room for human error with password protocols that makes it vulnerable to cyberattacks. And with passwords, it becomes almost impossible for IT or admin to determine an unauthorized entry until it’s too late.
To understand this better, let us look at how Simon logged in to his office network and how the use of passwords left his organization vulnerable to cyber theft.
The EAP-TTLS/PAP protocol supports (but does not require) server certificates to authenticate the client servers when a user is trying to connect to the network. However, what makes this protocol vulnerable is the use of passwords to authenticate the user and the process of delivering credentials/passwords over the air in “clear text,” and not as encrypted messages.
Let’s take a look at the other drawbacks of password-based authentication.
Disadvantages of Password-Based Authentication
Password Management is expensive and time-consuming
Password authentication as a process is expensive for the organization from both cost and time perspectives as well as the risk involved in data security. Good password management protocols, like resetting passwords periodically at an interval of 60/90 days and recovering forgotten passwords, require more manpower in the IT department. Also, the risk to data security is very high in case of cyber attacks as shown above in Simon’s organization. This leaves an organization vulnerable to losing business and reputation which carries long-term implications.
From a user standpoint, remembering, storing, and using passwords (multiple times to log in to different applications) is a tedious process that requires a lot of effort and often impacts productivity. As best practices, though changing passwords periodically is encouraged, it is a double-edged sword as too many passwords after a certain point becomes confusing and very often leads to accounts locking out for using the wrong passwords. This directly involves productivity as a user has to spend a good amount of time with IT departments to retrieve passwords.
Vulnerable to Cyberattack or Physical theft
Password authentication leaves an organization and its users vulnerable to cyber attacks since passwords are easy to steal. As our technology has become smarter so have the hackers. With cloud servers used for storing information, we may be able to protect the data from theft, but phishing, Man-in-the-middle attack (MITM), & over-the-air attacks give a hacker access to an account or at the very least allows them the opportunity to disrupt or stall work. Even if your employees are smart enough not to fall prey to phishing attacks, your network might still be vulnerable as some popular attacks (such as MITM) operate by fooling the device into automatically sending credentials to a spoofed network, without ever involving the human user.
Yes, with a strong password protocol, a hacker may not be able to access the cloud network, but the access they get to your local network to distribute different viruses can leave your network vulnerable to future cyber attacks. Any such attack requires every network user to reset and reconnect which becomes an arduous task for IT departments, a burden that often has a serious impact on the overall productivity of the organization.
What’s worse is there are no strong ways to identify the theft till the damage is already done since there is no way to verify the identity of the user when passwords are used to log in. The lack of solid ways to identify a user login with absolute certainty, especially for BOYD and cell phones is a threat that has no viable solution with password (EAP-TTLS/PAP) login.
Physical stealing too is not that difficult since all one needs to do is observe someone’s habits to understand where passwords are stored physically or connect with a disgruntled employee who might be willing to share their passwords. That is the reason most industry titans frown upon the use of passwords as a security measure.
Though your cloud servers may protect your data, however, the damage that such attacks can do to an organization’s reputation is often irreversible.
Access Management is Complicated with Password Authentication
Access management with password authentication is frankly still primitive in the sense that role-based access is a manual process with EAP-TTLS PAP. Let us go back to the example of Simon’s case to understand this a bit better. With an unsegmented password-protected network, a user has access to nearly all organizational resources whether they are required for a job role or not. If any files/folders have to be kept restricted, it is usually done by manually setting up more passwords to protect them. But that cannot be considered a robust technique since anyone with a password can access the network and can easily crack and access any file or folder they want or at the very least deploy a vast array of viruses that can leave your network crippled.
Had Simon’s organization used certificates to authenticate user login, both he and his company could have saved themselves the loss of reputation and data. Let’s see how certificate-based access works to keep the data safe from cyber-attacks or thefts.
Modern Passwordless RADIUS/AAA Authentication
EAP-TLS (Extensible Authentication Protocol-Transport Layer Security) provides centralized and individualized control over access to your Wi-Fi network. This protocol uses digital certificates utilizing a Public Key Infrastructure (PKI) to verify that a public key belongs to the user.
The users are provided login credentials that they use at the time of connecting to the network and the encryption keys are created and assigned in the background for every user session. Users do not actually deal with these encrypted keys and they cannot be copied or stolen from computers. The access can be modified or revoked by the IT administrator at any time and any changes in access are real-time meaning they become effective the moment a user authenticates using their login credentials.
Benefits of X.509 Digital Certificates for AAA Authentication
An X.509 certificate is a digital certificate that verifies a user or a machine passwordless. Below are some of the reasons that make the X.509 digital certificate the best standard for authentication.
Impenetrable Cryptography
Arguably the best feature of CBA is that certificates cannot be stolen or transferred and there is greater transparency as to who is accessing the information. When applied accurately, certificates provide robust security from over-the-air credential theft attacks like Evil Twin proxies and Man-in-the-Middle attacks. Unlike passwords, physical stealing of certificates is impossible as there is no way to transfer certificates since certificates are unique to each user/machine. This proves invaluable, especially for organizations that have BOYD culture or remote workers.
Role Based Access Management
802.1X allows admin to assign role-based access meaning a user will be provided access only to the information needed to perform their specific role. Organizations no longer have to worry about oversharing, and since revoking and reassigning new certificates involves just a few clicks on the admin’s part, the time and effort needed by the IT team is reduced by a substantial degree.
Better User Experience (UX)
Certificates provide a better user experience overall because they eliminate all the disadvantages that are faced when using passwords. We all have experienced the pain of remembering/storing passwords. The certificate-based authentication (CBA) process is completely automatic and does away with the wastage of time (for both the user and IT department) involved in what can be considered redundant activities like resetting or retrieving lost passwords.
With Single Sign On (SSO) users can efficiently authenticate to connected applications and services using a federated identity. SSO is probably the most visible authentication technology that relies on digital certificates.
Reduced Cost
802.1X, in the long run, can reduce your organization’s cost of managing a big IT department as password-related queries are completely done away with. Certificates make the process of authentication automatic, taking away a huge chunk of the workload from your IT department. Certificates eliminate issues related to password management like password retrieval, cyber theft, or cyberattacks that otherwise would have been a big and recurring problem that needed solving by your IT team.
| AAA Authentication with Password | AAA Authentication with 802.1x Certification |
|---|---|
| Expensive and time-consuming for IT Department | Single Sign On with X.509 digital Certificates makes Authentication Automatic |
| Vulnerable to Phishing,Over the Air attack, Physical Theft, and Layer 2 Attacks | Uncrackable Encryption |
| Access Management is manual | Role-Based Access Management |
| Difficult to Revoke Password Managed Access | Real-Time Control over Access Management |
| Difficult to Remember & Store Passwords & Susceptible to Human Error | Better User Experience |
| Password Login is a Non-Value add Process Step | Eliminates Credential Management |
Real-Time Access Management
Any changes made by the admin to the access provided like revoking a certificate are effective in real-time meaning, the changes become effective immediately when a user tries to authenticate. This comes in handy when a user’s role changes in an organization or in the case of physical stealing like in the case of Simon’s story. Had his organization used CBA to access their company’s network, the moment he intimated the theft of his mobile, his IT admin could have revoked his certificates to issue new ones, which would have prevented the data theft his company had to bear.
Migrating from EAP-TTLS PAP to Certificate-Based EAP-TLS Authentication Protocol
One might argue that setting up 802.1x is complicated due to the need for an AAA/RADIUS server and its complex configuration requirements, however, most organizations already use the back-end infrastructure (for example a Microsoft domain) that makes the whole setting up process effortless. Also, considering the risks involved with passwords, migrating to 802.1x authentication with WPA2-Enterprise encryption is well recognized as the most effective method of enterprise network security
The idea of a large-scale infrastructure overhaul might be a daunting thought, more so when considering the implementation. Especially for small and medium businesses, the thought of migrating might seem almost impossible given the cost of infrastructure and setup.
With SecureW2’s turnkey solutions, we can integrate your organization’s existing network infrastructure without the need for forklift upgrades. Our engineers are industry experts who can work with you to understand your requirements to tailor the services that best fit your needs. You can continue using your existing equipment and we will do the rest to fill the gaps.
We provide affordable services for organizations irrespective of size. To know more about our pricing, click here.