Can a RADIUS Server Authenticate a VPN
Due to the COVID-19 pandemic, more employees are working from home than ever before. The need to maintain network security has rightfully led many companies to utilize VPN to protect their remote workers.
VPN is a great first step, but it’s not an airtight security measure all by itself. To be truly secure using your home network, you’ll also need to use RADIUS authentication to access that VPN.
Why Use a VPN for Remote Access?
The primary reason organizations implement VPN isn’t actually for the encrypted tunnel or traffic masking that a VPN provides – it’s usually to allow remote devices to be “virtually present” so they can connect to the on-premise network and the resources contained therein. This setup is called a VLAN (Virtual Local Area Network).
In these instances, the security benefits of a VPN are secondary – it’s a nice bonus, but it’s probably redundant because the host network is already protected with WPA2-Enterprise or similar.
Equally important as the encryption is group policies. Every sysadmin knows that security vulnerabilities aren’t just present on the perimeter of your network, they can also be internal. Every employee is a possible vector of attack, through negligence if not malicious intent. That’s why employees need to be categorized into groups that have different levels of permissions – to limit the damage any user could potentially cause.
In normal circumstances, group policy and user segmentation are handled in the background by the PKI. However, depending on the configuration and capabilities of your firewall and access points, this infrastructure may not be operating correctly. Indeed, some VPNs don’t have the ability to reference your user directories at all.
VPN VS. RADIUS
The solution to the above issue is simple – use your RADIUS for VPN authentication..
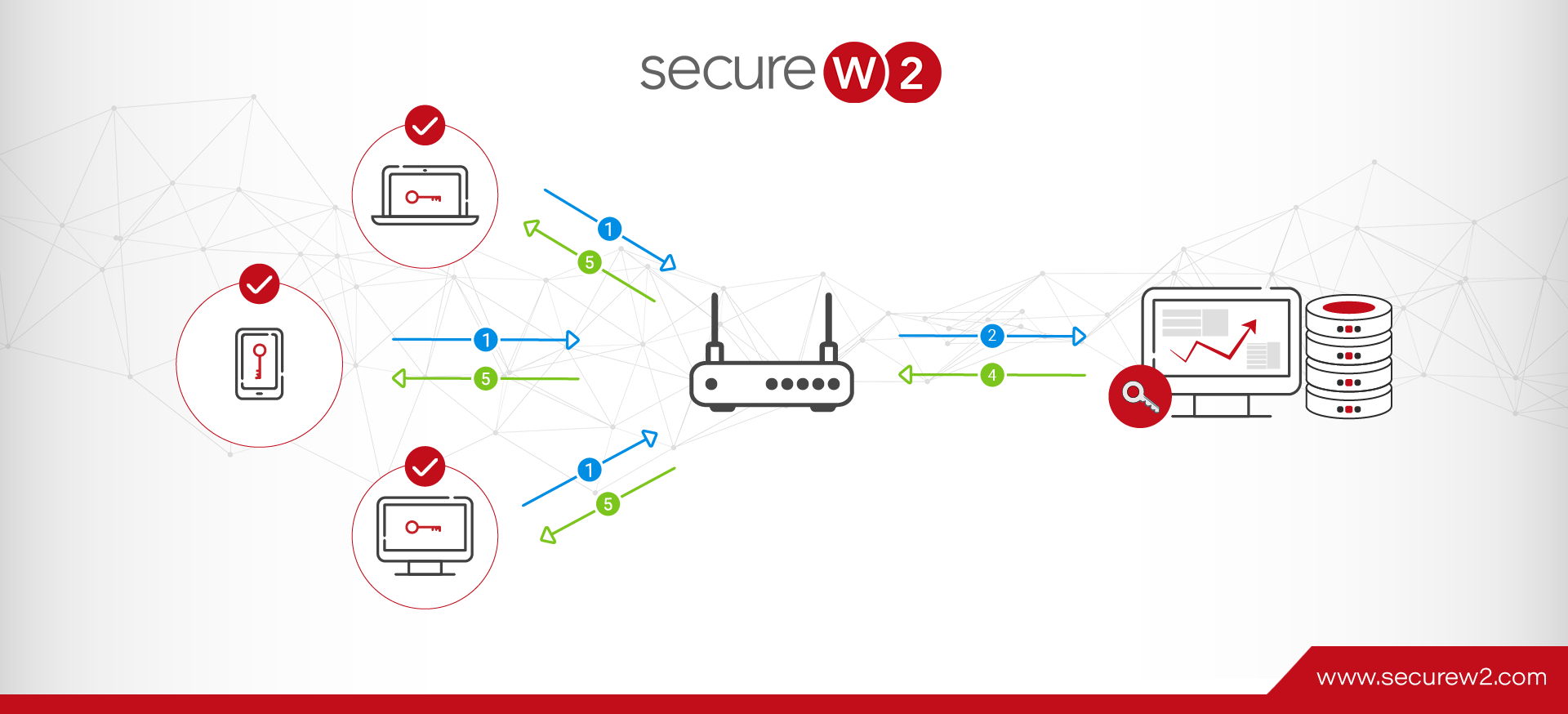
Yes, you can use your organization’s RADIUS to authenticate remote users. By configuring the VPN to connect to your office access point, the remote device can be “virtually” present and be authorized even by an on-premise RADIUS… though Cloud RADIUS services are easier and more secure.
The benefits of using your RADIUS in conjunction with VPN for remote access are twofold:
- It’s more secure. After the VPN connects to your office access point, the users undergo RADIUS authentication for network and resource access. Doubling up on protection keeps your traffic safe at all stages of the process.
- If your firewall, access point, or VPN doesn’t support user attributes or directory referencing, you can still use your RADIUS to implement security policies.
In fact, using your RADIUS to authenticate your users instead of a VPN is the security best practice no matter the situation. You don’t leave your network security to a third party in normal circumstances – why would you start now? This method ensures that ultimate control is still in your hands.

RADIUS Servers are Versatile Security Tools
While we’re on the subject of implementing RADIUS, you might be interested to know about the other ways it can strengthen and streamline your security processes.
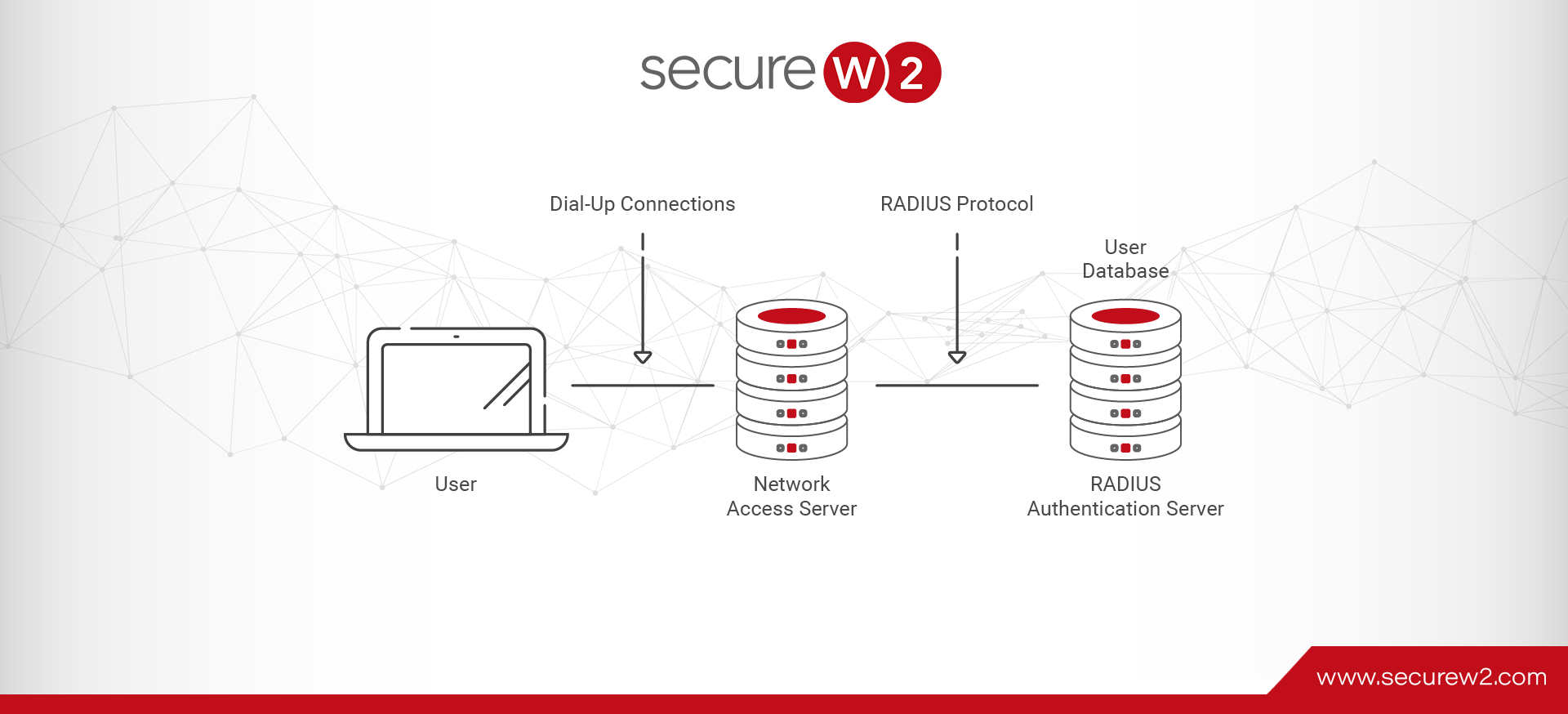
RADIUS isn’t just useful in a work-from-home setting. The standard RADIUS use-case is to quickly and easily connect users to Wi-Fi. The most secure iteration of RADIUS uses the EAP-TLS authentication protocol to authenticate users with digital certificates instead of credentials.
Once users have been enrolled for a certificate, the RADIUS server can use that to verify the level of permissions they have. You can create group security policies to segment users into different levels of resource access, controlling who has access to Wi-Fi, VPN, and other resources.
After that, it’s simply a matter of keeping the user directory updated; no need to manually enter user details into your VPN or gateway.
Cloud RADIUS especially is a set-it-and-forget-it solution to network security… and it’s not as difficult to implement as you might think. We can integrate with your existing network infrastructure or help you build a secure network from the ground up in no time at all. Even better, we have affordable pricing for organizations of all sizes. Click here to see our pricing.