Why Is An Evil Twin Attack Harmful To Your Network?
The U.S. Department of the Interior’s (DOI) internal IT Wi-Fi system was attacked by white hat hackers in 2020 using an “evil twin” spoof and a $200 homemade hacking kit. They gained access to the internal data and employee credentials that let them access all open tickets within the organization.
A report submitted by the DOI stated that the testers attacked the network using stolen credentials by “evil twin” hacking to access the secure network. Using the “evil twin” technique, they created a new access point and gave it the same name as the original one.
Subsequently, the hacker can lure a user into connecting to a network using the fake access point, giving the hacker access to data. The breach even leads to the whole department shutting down and fixing their network in three weeks with secure means like VPNs.
Are you worried that this could happen to you? Read on to learn more about evil twin attacks, how they are orchestrated, and how to protect your network from them and keep your essential data safe.
What Is an Evil Twin Attack?
When traveling, in an airport, or just sipping your favorite coffee at a cafe, you will likely connect to free Wi-Fi to check your messages and browse the internet. Suppose you see an unsecured connection with a familiar name of a nearby cafe or hotel tempting you to connect. In that case, an evil twin network may try to lure you and hack into your data with mischievous intent.
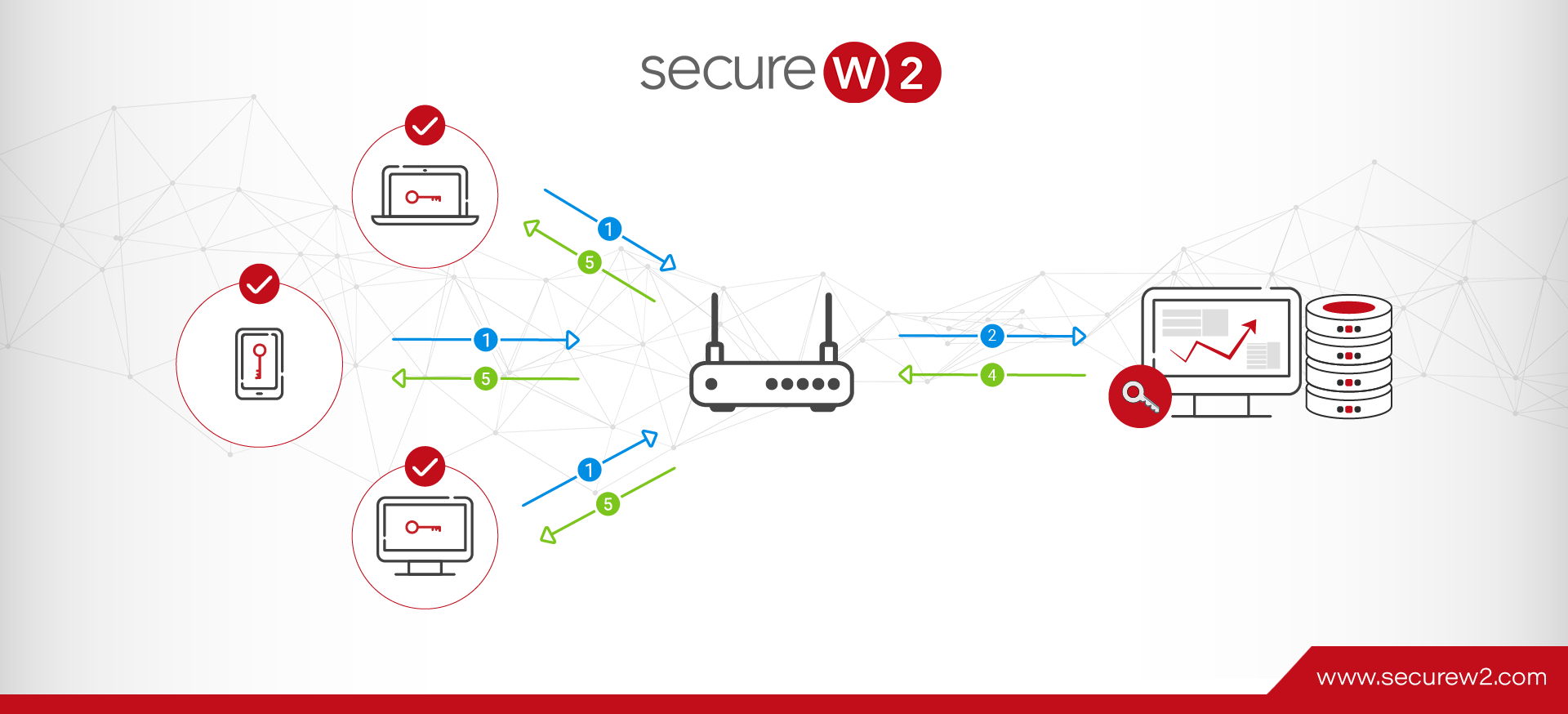
An evil twin attack is what it sounds like: an evil Wi-Fi network twin. The attacker sets up a fake access point and expects the user to connect to it rather than the real one. When the user connects to the network with the fake ID, the hacker gets access to all the data the user shares through this access point.
The evil twin Attack is a hazardous form of a man-in-the-middle attack, as it is impossible to identify the malicious network with its innate ability to spoof the original network.
How Is an Evil Twin Attack Orchestrated?
A typical evil twin attack works as follows:
- Identifying the best location
- Setting up the rogue Wi-Fi access point
- Luring victims to connect to the rogue point
- Stealing the data shared by the victim
Identifying the Best Location
The hacker typically looks for an unsecured network connection or something with a vulnerable password and multiple access points with the same name. This makes the fake ID easier to set up and almost impossible to detect. The hacker can set up shop in a network close to their targeted access point to access the network. An evil twin attack is very easy to conduct. It has the following prerequisites:
- An access point with monitor mode capabilities. Wi-Fi pineapples are a standard tool used for this purpose.
- A Linux machine.
- EAP Hammer is a tool that can be installed on the machine for free.
- Password cracking tools like John the Ripper or HashCat.
- A FAKE digital certificate will be used as the RADIUS Server Certificate
- A physical location in a range of the target network. Many hackers can sit in a public business nearby, such as a coffee shop or restaurant.
Setting Up the Rogue Access Point
The hacker cracks the legitimate Service Set Identifier (SSID) to set up a new rogue account from the original network with the identical SSID. A fake SSID can be created from a smartphone, portable router, or tablet.
A device called a Wi-Fi Pineapple is also used to reach a broad range, and a device that connects to the Wi-Fi can’t differentiate between the real and fake one.
Luring Victims to Connect to the Rogue Point
To lure a victim, the hacker moves closer to the victim and creates a stronger connection. This would automatically lure the user into connecting to a more robust network for their device.
Stealing the Data the Victim Shares
Once you log in to the evil twin network via a hacker, they can monitor all user activity like social media or access to your bank accounts. If a user logs in to any of these accounts through a single set of credentials, the hacker would inadvertently gain access to all the user’s accounts accessed with those credentials.
Consequences of a Successful Evil Twin Attack
How to Spot an Evil Twin Attack
Several indicators point to an evil twin attack. The most common indicator is an Access Point (AP) set up with a real AP nearby. Another standard indicator is that an AP broadcasts a different channel from the genuine AP. A fake AP would also have weaker encryption.
Another indicator of a fake AP would be the number of user devices that are connected to it. If more end-users connect to the AP than they should, they could also be connected to a fake AP.
The Aftermath of an Evil Twin Attack
The attack begins when the hacker steals your Wi-Fi credentials. After obtaining your credentials, a hacker can launch a series of attacks like:
- Attack surface expansion uses a compromised device that scans the network for other vulnerable devices and users.
- Lateral movement, in which the hacker uses a compromised device and gains access to other devices.
- Privilege escalation involves the hacker elevating privileges on a device by gaining root access through a device’s operating system or apps.
- AD exploitation is when the hacker exploits vulnerabilities in Active Directory to access other user credentials.
- DoS or the Denial of Service attack, in which the hacker shuts down a whole network, making it inaccessible to its intended users. This involves jamming the network with an influx of requests that overwhelms it, stops productivity, and raises security concerns.
In the aftermath, an attacker can now access the network and user credentials or at least one of the two. Once they get access, they can target other devices like IoTs to harvest further credentials. Users tend to make minor changes to existing credentials, making them vulnerable. A hacker can use them to attack and access cloud services like Azure AD.
How to Protect Yourself From Evil Twin Attacks
An evil twin attack can severely threaten your network as it is easy to orchestrate and untraceable. The steps below ensure you can effectively mitigate the risk of an attack on your network.
- Connect to a legitimate Wi-Fi network. Contact your administrator for accurate credentials if you are unsure about the network.
- Do not use public Wi-Fi networks. If you need to connect to a public network, use Passpoint or a VPN to protect your data from malicious eyes.
- Be prudent. If you see a network with a similar name or a network that does not require a password, it’s better to stay away and not connect to it.
- Use a more robust form of security like digital certificates instead of passwords for stronger data encryption.
- Disable any unnecessary access points and ports on your network to reduce the risk of unauthorized access through vector attacks.
Deploy Digital Certificates for Better Network Security
A credential-based network is always at risk of modern cyber threats like MITM and evil twin attacks. Passwords are still difficult to manage and insecure as they risk being cracked, stolen, and misused. Businesses are slowly moving towards more secure forms of passwordless authentication like MFAs and digital certificates.
MFAs are considered safe and acceptable. However, the user experience leaves a lot of gaps. MFAs still rely on credential-based authentication or devices, which are tedious and time-consuming.
Digital certificates, on the other hand, offer a better experience for the user and the administration. Certificates reduce considerable time and manpower as they can be downloaded once and stay until they are revoked.
Certificates are unique and cannot be stolen or used on another device or user. They use private-public key encryption, making them more secure than passwords. Certificates also reduce the number of IT tickets by keeping the network secure and allowing users to experience seamless connectivity.
Minimize Chances of Attacks With SecureW2’s Network Security Solutions
SecureW2 offers a robust cloud-based solution to eliminate the need for passwords and leverage digital certificates to secure your network. Leave unsafe PSK behind with our managed PKI and RADIUS solutions that will integrate with your existing infrastructure.
In the past, doing 802.1X with EAP-TLS in the cloud securely has been tedious for administrators. With SecureW2, the transition is quick, simple, and secure. You can streamline certificate issuance through a top-rated self-service onboarding technology for unmanaged devices or gateway APIs for managed ones.
Talk to our experts today to discover how our solutions can help you go passwordless.