Credentials vs. Digital Certificates For RADIUS Authentication
As an organization scales, there will eventually come a point when a pre-shared key is no longer sufficient for controlling network access. Whether to manage multiple locations or simply to accommodate the growing number of employees, a security-conscious company will eventually need to upgrade to WPA2-Enterprise for their networking needs.
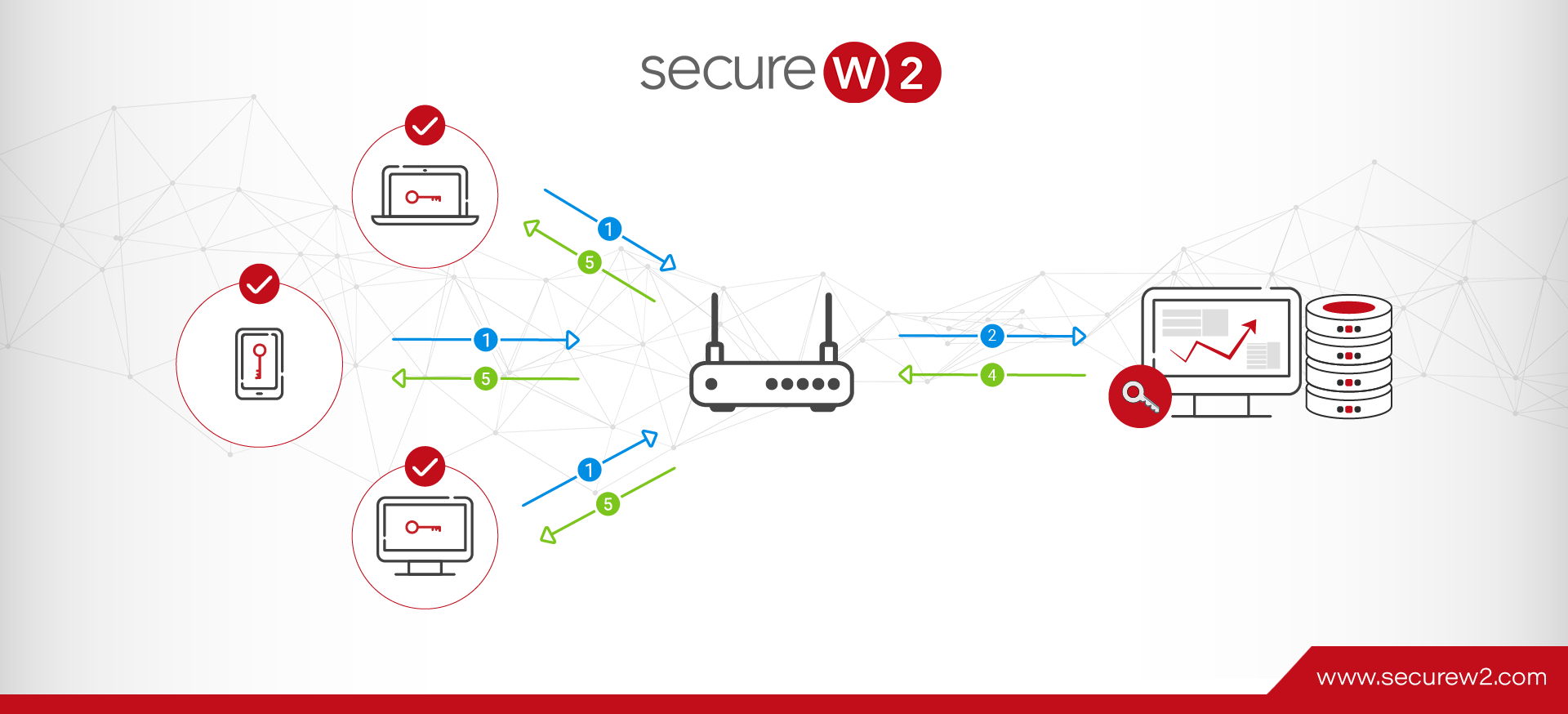
A RADIUS server is the core component that facilitates a WPA2-Enterprise network. It handles authenticating users via the chosen 802.1x policy. The biggest decision you need to make during this upgrade process is which flavor of EAP you will be implementing.
RADIUS Server Authentication with Credentials
Practically speaking, security is typically a compromise between convenience and protection. If credentials were placed on that axis, they would lean far towards convenience.
Credentials, typically a username and password, have been the standard of authentication for years, even though they’re mostly insufficient.
Credentials Are Not Reliable for Identity
Credentials rely on ever-fallible humans to remember the username and password and keep it secret, and people are pretty bad at both of those things. The best password in the world is utterly useless if the user falls prey to a phishing scam… not to mention the best password would be practically impossible to remember.
Networks Are Bypassed Using Stolen Passwords
Even if a person doesn’t do anything wrong, credentials can be stolen in over-the-air attacks. A clever hacker can spoof the router or access point and your device will automatically submit the login credentials to the false access point – handing them the keys to your network.
Two of the most common 802.1x policies, EAP-TTLS/PAP and PEAP-MsCHAPv2, can only support credentials.
RADIUS Server Authentication with Digital Certificates
Certificates are widely known to be far more secure than credentials but are often mischaracterized as being complicated or difficult to implement.
Improved Identity Management with Certificates
Certificates are analogous to a driver’s license or other picture ID. They tie the name/identity of a person/device to the authentication, meaning the network knows exactly who and what is authenticating.
That alone has a number of advantages. Namely, it creates accountability for employees using the network – it eliminates the plausible deniability that shared accounts and shared passwords provide.
Stronger Defense Against Over-The-Air Credential Theft
Even more important is that it makes certificates the best defense against both phishing and over-the-air attacks. There are no credentials to leak to phishers and even if a hacker manages to intercept your data during authentication, they’d lack the private key that positively identifies the owner of the certificate – rendering it useless.
The increased security is all well and good, but what’s it like for the end users that need to use certificates on a daily basis? Much better, actually.
Improved User Experience
The user experience for certificates is effortless compared to credentials. There’s no need to remember a username and password. There’s no need to reset your password every 90 days or so in a misguided attempt to maintain security. Certificate lifetimes can be customized by the organization, but it’s common for them to remain valid for upwards of 5 years.
Certificate Authentication with Cloud RADIUS
The only 802.1x authentication protocol that supported certificates is EAP-TLS – the most secure option.
Our Cloud RADIUS servers can integrate with any network infrastructure, but we highly recommend using EAP-TLS with certificates. If you’re lacking the PKI necessary to implement certificates, our parent company SecureW2 provides the necessary components to integrate into your current infrastructure without the need for forklift upgrades.
Network security isn’t a “good enough” purchase. Don’t settle for less than the best – utilize Cloud RADIUS’s certificate-based authentication to enhance the user experience and overall security. Click here for more info on pricing.