Secure Authentication With Cloud RADIUS
To accomplish this, many organizations seek identity context with an effective IDP, like Okta, and combine it with FreeRADIUS. Many organizations have found the combination of FreeRADIUS and Okta to be sufficient for their authentication security needs, but other security options exist that may be better suited to protect your network against the diverse and ever changing authentication landscape.
How to Authenticate Okta Requests with FreeRADIUS
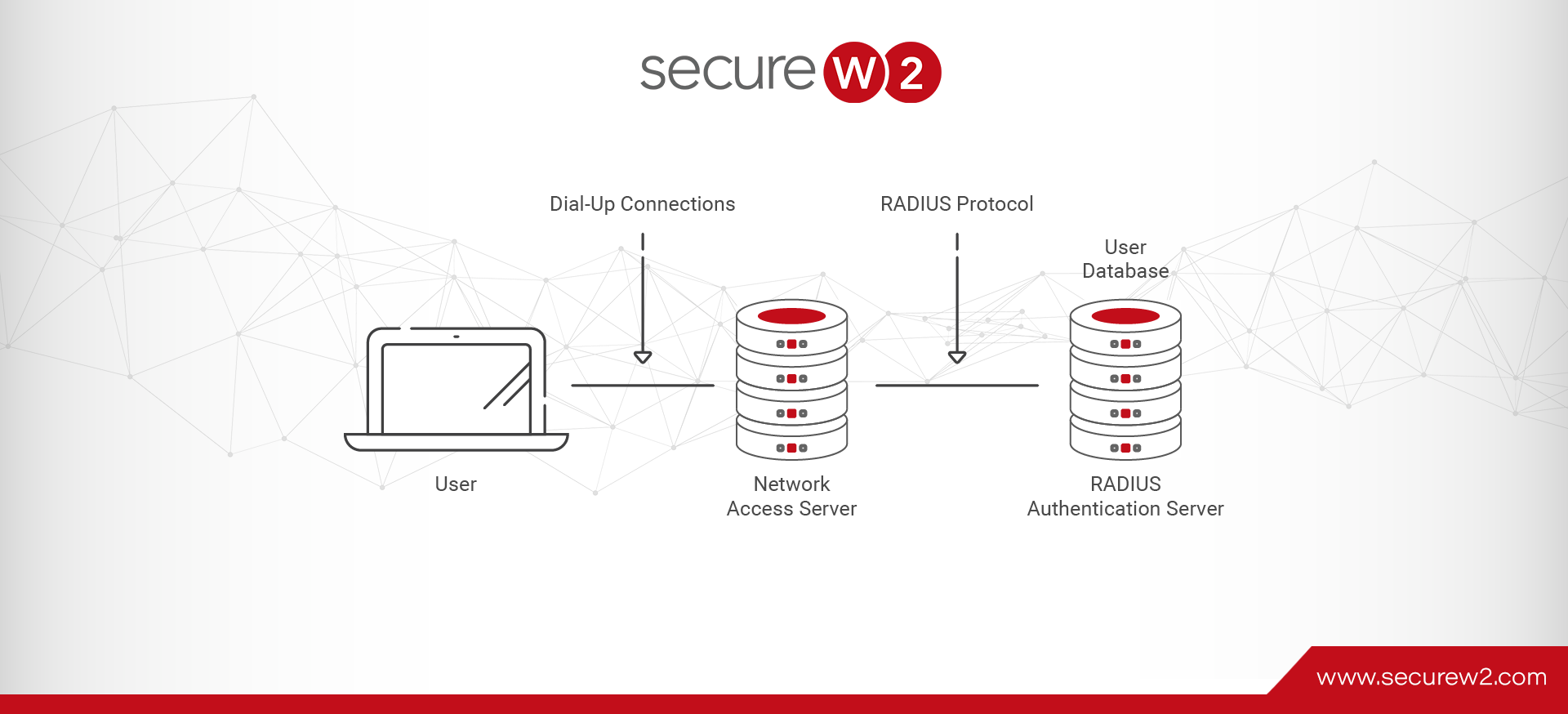
The process of authenticating an Okta directory user through the FreeRADIUS client is straightforward, as most RADIUS authentication processes are.
Depending on your authentication setup, the user sends the RADIUS their authentication identity – often credentials. If the organization uses Multi-Factor Authentication (MFA), a valid set of credentials will move them along in the process and prompt a second authentication factor.
Simply put, if they are a valid Okta user and present the correct authentication materials, they will be authenticated for network access. Unfortunately, protecting this process is not as simple, and there are countless instances of authentication fraud.
802.1x Authentication Security for FreeRADIUS
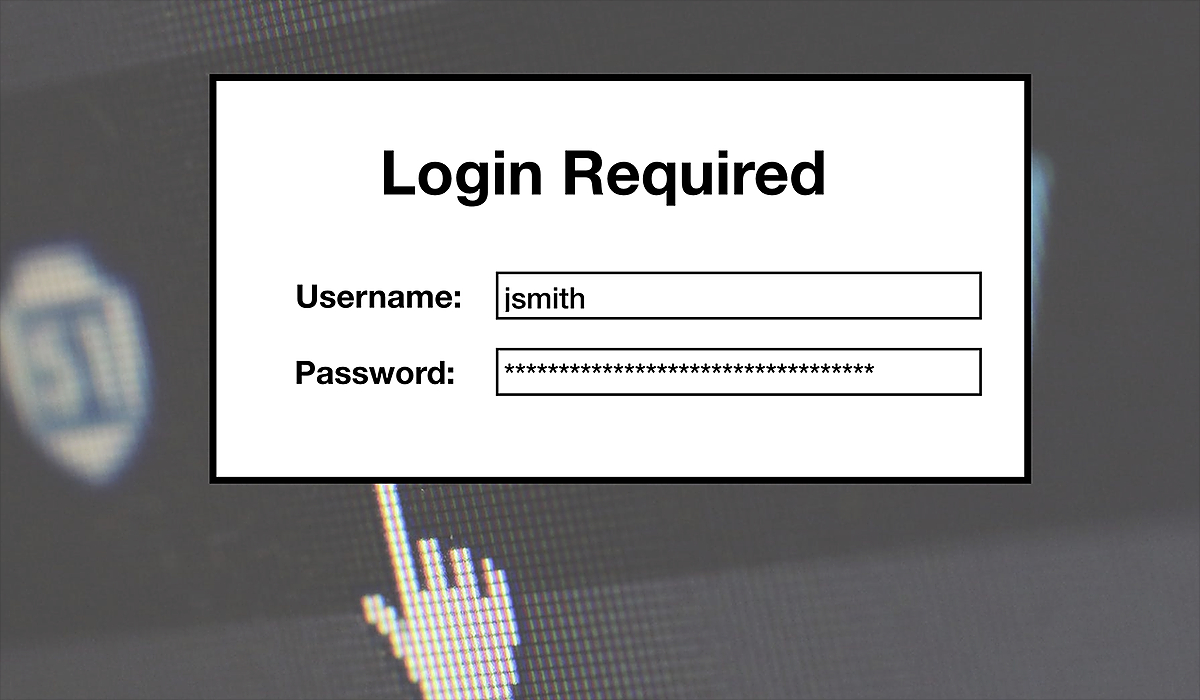
When it comes to authentication security, many organizations are quick to jump to credential-based authentication, but time and again credentials have shown to be inadequate. They are easily stolen or cracked and rely heavily on the user, which is the weakest link in the cybersecurity chain.
More security-conscious organizations have turned to MFA, which requires 2 or more forms of identification to approve network access. While MFA is highly effective in blocking a vast array of attacks, the use of credentials is still a detriment. As an alternative to credentials, many have been implementing the gold standard of authentication security: digital x.509 certificates.
Distributing certificates to network users and configuring FreeRADIUS for EAP-TLS authentication is a huge security advantage over credentials. By utilizing public key cryptography, certificates cannot be replicated by outside attackers, and EAP-TLS authentication protects against over-the-air attacks.
With the stronger security afforded by certificates comes the price of added complexity. Configuring certificates manually can be difficult, and this is compounded by the huge number of devices owned by network users and diversity between them.
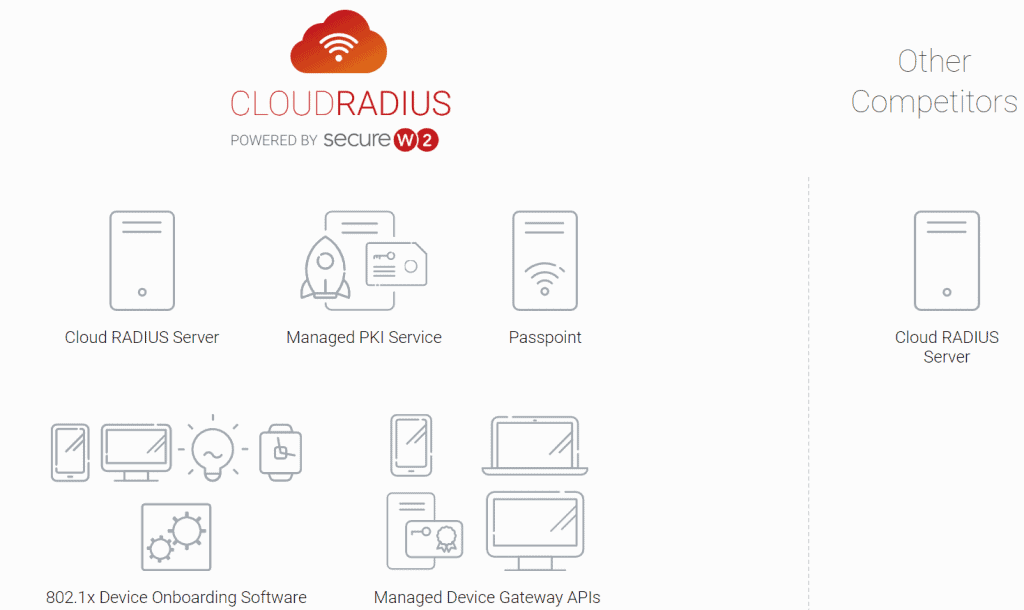
This highlights the importance of vetting a potential vendor to find if they are up to the task of provisioning certificates. PKI vendors offer different capabilities when it comes to a smooth integration with your network.
Perhaps the most important capability that an organization should look for is an effective onboarding solution. Requiring your IT department to distribute certificates manually is a slow process, and leaving the task up to the average network user will inevitably result in endless IT support ticket requests.
Additionally, setting up a PKI is a task that many organizations find difficult to complete on their own. A standup PKI is costly to configure and maintain over time, and finding an effective vendor can be difficult when so many have different levels of security and usability.
A Certificate Authentication Solution for Okta
While you can configure Okta to populate your certificates with user information and authenticate them via FreeRADIUS, there are more efficient solutions. It will be difficult to distribute certificates for this configuration, and it will be an intensive, ongoing management process.
SecureW2’s certificate solutions easily integrate with Okta (or any cloud IdP) while providing everything needed for an efficient, certificate-based network. Our Cloud RADIUS and turnkey PKI can be quickly incorporated into any network infrastructure and have your network ready to distribute certificates in mere hours. Our PKI solution is HSM-protected and can distribute certificates to BYOD, IoT, and MDM.
The JoinNow onboarding solution is designed to be completed quickly and easily by network users of any technological literacy level. The process requires a few basic steps and as little as one minute of time to be distributed a certificate that can effectively authenticate for years.
JoinNow is also vendor-neutral and easy to manage from an IT standpoint. Our management portal and certificate management tools allow you to view configuration and authentication events in real-time. It also provides the capability to remotely diagnose and resolve connectivity issues.
The Best Okta Authentication Solution
Authentication security is at the forefront of cybersecurity and is the first line of defense against outside intrusions. Without an effective method to regulate who has network access, your directory and valuable data can be easily manipulated and stolen for a profit. While FreeRADIUS provides strong authentication security, it falls short when it comes to network management and ease of use.
SecureW2’s certificate solutions are the best tool available for your MFA solution and guarantee no outside actors will be able to access the network. Check out our pricing page to see if our certificate solutions are the right fit for your organization.