
What Is ARP Poisoning?
ARP poisoning is a malicious attack method hackers use to interrupt network connectivity by manipulating the Address Resolution Protocol (ARP). An attacker may exploit several security flaws if they can mislead network devices into associating wrong IP addresses with MAC addresses via the use of forged ARP packets.
The importance of learning about and fixing ARP poisoning is enormous. The effects of this kind of attack, such as the theft of private data, the eavesdropping of network traffic, and the possibility of future exploitation, may be devastating. Attackers may perform traffic rerouting, packet interception, and even man-in-the-middle assaults by compromising a network’s ARP tables.
In this article, we’ll investigate ARP poisoning in detail, diving into its nuances, attacker approaches, and, most crucially, ways to defend against and circumvent such assaults. We’ll start with the basics of ARP to ensure you have a firm grasp of the subject.
Understanding ARP at a Higher Level
To understand ARP poisoning, you must know what ARP (Address Resolution Protocol) is. ARP helps connect a network’s logical and real addresses. People can better understand how ARP poisoning takes advantage of flaws if they know what it is used for and where it is weak. This information helps protect networks and figure out where security risks are.
What Is ARP?
A critical protocol for facilitating device communication in computer networks is the Address Resolution Protocol (ARP). Resolving or mapping logical IP addresses to their corresponding physical MAC addresses is its main purpose. Because devices on a network interact with one another using MAC addresses at the data link layer and IP addresses at the network layer, this translation process is crucial.
Here is a more thorough description of how ARP functions:
Each device on a network has a distinct IP address that acts as its logical identification, along with a MAC address. Each device also has a MAC address, a globally unique physical identification burned into the network interface card (NIC), which is another feature.
ARP table: A device initially examines its ARP table when it wants to interact with another device on the same local network. The IP-to-MAC address mappings for the devices it has recently talked with are shown in the ARP table. If the destination IP address is located in the ARP table, a direct connection is made using the matching MAC address.
ARP Request: The device starts an ARP request if the destination IP address is not already in the ARP table. It asks, “Who has this IP address?” by broadcasting an ARP request packet with the IP address it wishes to connect to. This broadcast is received by all local network-connected devices.
ARP Response: The device that matches the requested IP address will send back an ARP reply packet in response that includes its MAC address. The device that sent the ARP request will get this answer directly.
ARP Cache: The asking device changes its ARP table with the IP-to-MAC mapping after receiving the ARP reply. By eliminating the need for repeated ARP queries and accelerating network transmission, this mapping is stored for later use.
ARP Timeout: Known as the ARP timeout, the ARP cache entries have a limited lifespan. After this period, the record is deleted from the cache and, if necessary, a fresh ARP request is sent.
Devices can easily locate and communicate with one another thanks to ARP, which is a basic and crucial component of local network communication. However, because of its simplicity, it is also susceptible to assaults like ARP poisoning, in which hostile actors trick the ARP process to illegally intercept or reroute network communications. Network administrators must be knowledgeable about ARP in order to efficiently maintain network security and handle connection difficulties.
What Is an ARP Message?
The ARP protocol allows devices to share information about IP and MAC addresses via messages. ARP relies heavily on these messages to function correctly since they are used to create and modify IP-to-MAC address mappings.
Broadcast Address Resolution Protocol (ARP) messages are used to discover or reveal IP and MAC addresses on a network. Specific fields in these communications provide information critical to proper address resolution. To resolve an IP address, devices employ the Address Resolution Protocol (ARP) for both requests (Who-has) and reply (Is-at) operations.
There are several parts of an ARP message, and they all do something meaningful. These are the five required pieces of information in an ARP message:
- Source MAC address
- Source IP address
- Destination MAC address
- Destination IP address
- ARP operation code
By analyzing these parts, devices may update their ARP cache and keep their IP-to-MAC address mappings correct.
The Relationship Between ARP, IP Addresses, and MAC Addresses
To fully grasp how ARP poisoning attacks function and the significance of precise IP-to-MAC mappings, it is essential to have a firm grasp on the interplay between ARP, IP addresses, and MAC addresses.
ARP is a protocol that converts between IP addresses and MAC addresses. It facilitates communication at the data-link layer by allowing devices to map IP addresses to physical network interface cards. ARP improves the efficacy of network communication by ensuring that data packets are sent to the correct hosts by resolving IP-to-MAC address mappings.
To provide safe and effective network communication, precise IP-to-MAC address mappings are required. ARP poisoning attacks cause data corruption, privacy leaks, and unauthorized access to network resources by injecting inaccurate mappings. To guarantee the dependability and efficacy of network operations, it is essential to keep IP-to-MAC mappings in good shape.
Deep Insight Into ARP Poisoning
ARP poisoning is a nefarious method utilized by malicious actors to manipulate the Address Resolution Protocol (ARP) within a computer network. Through the strategic exploitation of the inherent weaknesses within the Address Resolution Protocol (ARP), malicious actors have the capability to cunningly manipulate network devices, thereby forging an association between their Media Access Control (MAC) address and an alternate Internet Protocol (IP) address.
This facilitates the capability to intercept, alter, or divert network traffic, thereby resulting in potential security vulnerabilities, unauthorized data exfiltration, or illicit system entry. It’s vital to thoroughly understand the ARP poisoning concept to effectively identify and counteract such malicious attacks, thereby fortifying network security and safeguarding critical data.
Introduction to ARP Poisoning
If you want to trick devices on a network, you may use a malicious attack method called ARP poisoning. By sending bogus ARP packets, the attacker may deceive the victim’s devices into assuming that a specific IP address belongs to a MAC address that isn’t associated with that IP.
ARP poisoning is primarily used to obtain unauthorized access to networks and data or to start other forms of cyber assaults.
ARP poisoning attacks may be understood better if one considers the many reasons behind them. ARP poisoning is often used to achieve the following goals:
- An attacker’s goal while attempting to eavesdrop on a network is to get private information such as passwords, financials, or the contents of private business conversations.
- Intercepting, modifying, or injecting malicious material into communication between authorized devices is called a “man-in-the-middle attack.” This is possible if an attacker can access the network’s ARP tables.
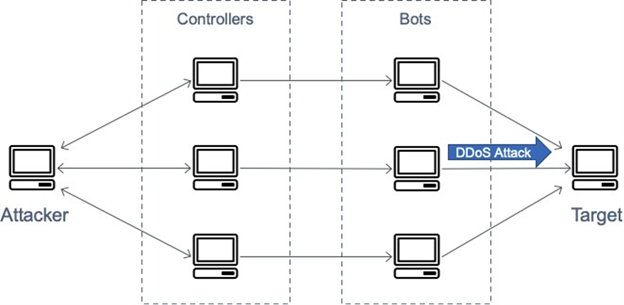
- By flooding the network with spoofed ARP messages, generating conflicts, and leaving devices unable to connect efficiently, ARP poisoning may also be used as a Denial of Service (DoS) attack.
Techniques Used in ARP Poisoning
There are various methods for launching an ARP poisoning assault, each with a unique strategy and degree of difficulty. Attackers often use these typical techniques:
- ARP Cache Poisoning: To associate their MAC address with the IP address of an actual device, attackers transmit fake ARP responses to update the ARP cache of target devices. Attackers may now monitor and alter all network traffic.
- MITM Attacks: By inserting themselves between the transmitter and the receiver, attackers may eavesdrop on and alter data packets without raising suspicion.
- ARP Spoofing: Attackers transmit forged ARP packets, attempting to take control of a device’s IP address already in use. This causes disruption and chaos inside the network, which the attacker might use to their advantage by intercepting and manipulating data transmission.
Types of ARP Attacks
Different varieties of ARP attacks have different features and repercussions. The following are examples of common forms of ARP attacks:
- Standard ARP Poisoning: Most ARP poisoning attacks work like this, with the attacker manipulating the ARP tables to reroute traffic and intercept packets.
- Reverse ARP Poisoning: In this variant, the attacker’s MAC address is used to trick the gateway router into thinking that the actual IP addresses of the network devices belong to the attacker.
- Gratuitous ARP Attacks: To wreak havoc on a network, hackers will send out forged ARP announcements that incorrectly map IP addresses to MAC addresses.
To effectively deploy countermeasures and defend networks from possible vulnerabilities, it is essential to have a firm grasp of the many forms of ARP attacks.
Preventing ARP Poisoning
Importance of Preventing ARP Poisoning
Given the severity of the possible outcomes from ARP poisoning attacks, safeguarding against them must be a top priority. Organizations can significantly lower their risk of falling prey to such assaults by deploying stringent security measures.
Among the many reasons why avoiding ARP poisoning is crucial are the following:
- Safeguarding Confidential Data: By thwarting ARP poisoning, sensitive data like passwords, bank account numbers, and IPs may be kept out of the wrong hands.
- Ensuring Network Integrity: Organizations may protect their network infrastructure and keep devices talking to one another safely and reliably by foiling ARP poisoning efforts.
- Reducing the Risk of Secondary Attacks: By closing the security holes that ARP poisoning opens, cyberattacks like man-in-the-middle assaults and data eavesdropping may be avoided.
Techniques to Prevent ARP Poisoning
- Implementing Secure Network Protocols: By monitoring and validating ARP messages, secure network protocols like ARP Inspection may help stop ARP poisoning attacks by ensuring that only valid ARP answers are received.
- Network Segmentation and Isolation: By segmenting the network and isolating vital nodes, it is possible to lessen the damage caused by ARP poisoning assaults. Organizations may improve network security by restricting attackers’ ability to modify ARP tables.
When it comes to network segmentation, SecureW2 has been at the forefront of innovation with our policy engine. Our solution works with a wide variety of vendors, and it provides efficient methods for putting vendor-specific network isolation plans into action. This aids businesses in increasing their network security by enforcing stringent, customizable safeguards against ARP poisoning attacks, and it does so by implementing relevant network policies.
- Monitoring and Detection Systems: To respond quickly and mitigate such attacks, it is helpful to have network monitoring and intrusion detection systems that can identify and highlight abnormal ARP behaviors.
- Network Security Best Practices and Policies: Reduce exposure to ARP poisoning attacks using network security best practices such as frequent patching, robust authentication methods, and staff education. In addition, it is essential to practice security policies that establish and implement stringent network access control procedures.
ARP Spoofing vs. ARP Poisoning
Although the terms are sometimes used interchangeably, ARP spoofing and ARP poisoning are different methods of altering the Address Resolution Protocol. To successfully handle the related risks and execute suitable countermeasures, it is essential to have a firm grasp of the distinction between the two.
ARP Spoofing: Sending forged ARP messages is called “ARP spoofing” in the networking world. The attacker pretends to be another device on the network by saying they have a specific IP address and linking it to their own MAC address. The attacker can then snoop on, alter, or otherwise monitor the data that is supposed to reach the victim’s device through the network.
ARP Poisoning: In a larger sense, ARP poisoning refers to any manipulation of the ARP tables intended to mislead network devices. It can be interpreted as a more all-encompassing attack that uses ARP spoofing. Attackers use ARP poisoning to trick devices into associating wrong MAC addresses with IP addresses by injecting bogus ARP messages into the network. By tampering with ARP tables, hackers can interrupt regular network operations and launch other forms of cyberattacks.
The Role of Zero Trust in Minimizing ARP Poisoning
The risk of ARP poisoning attacks may be greatly reduced in large organizations by using a security architecture like Zero Trust. Zero Trust models start with the premise that every user, device, and component of the network is inherently untrusted, as opposed to the more typical perimeter-based models. A fine-grained system of access controls is in place to guarantee that only authorized parties have access to any given resource. Attackers are less likely to be able to alter ARP entries using this method.
For Zero Trust to succeed, strong identity and access control solutions must be used to verify the identities of network clients and devices. Strict authentication procedures may protect against ARP poisoning attacks by preventing unauthorized changes to ARP tables. As the backbone of Zero Trust, a PKI provides encryption, digital certificates, and safe key management to fortify the security of a network further.
SecureW2, an industry leader in network protection, provides helpful advice on how to implement PKI in Zero-Trust networks. The information in these sources may help businesses protect themselves against threats like ARP poisoning and keep their most sensitive data safe from prying eyes. By adopting Zero-Trust practices, businesses have the ability to create a robust network architecture that puts security first and foils threats.
Empowering Network Security With VPN Solutions
ARP spoofing and ARP poisoning are two vulnerabilities that must be identified as soon as possible and fixed to keep a network safe in today’s linked world, where cybersecurity threats are constantly developing. Organizations can take preventative actions to protect their networks and private information if they know the distinctions between ARP spoofing and ARP poisoning and the unique dangers posed by each method.
Implementing a Virtual Private Network (VPN) is one efficient approach to enhance network security and avoid these assaults. SecureW2’s VPN solutions are reliable, offering encrypted connections to keep hackers out of your network. Discover how SecureW2’s VPN solution can strengthen your network’s defenses.
Also, with our Cloud PKI solution, you can be confident that only approved users and devices can access your network’s apps and data. Our Cloud RADIUS and PKI products allow you to track every device and user on your network, divide users into groups according to their permissions, and implement stringent security policies.
You can significantly strengthen your network’s resistance against ARP spoofing, ARP poisoning, and other cyber threats by taking a preventative stance on network security, using VPN solutions, and applying zero-trust principles with SecureW2’s Cloud PKI services. Don’t put off until tomorrow what must be done now to protect your network and guarantee the safety of your most important information and assets.
Get in touch with us today to find out how SecureW2 can help you protect your network.