How to Setup a Windows RADIUS Server
Table of Contents
- What Is a Windows RADIUS Server and How Does NPS Fit In?
- Prerequisites for RADIUS Server Windows Setup
- How to Set Up a RADIUS Server on Windows: Step-by-Step
- Common Windows RADIUS Errors and How to Fix Them
- Windows NPS Limitations: Why IT Teams Move to Cloud RADIUS
- Frequently Asked Questions
Pre-shared key networks expose organizations to credential theft and over-the-air attacks. Windows Server’s Network Policy Server (NPS) is Microsoft’s built-in Remote Authentication Dial-In User Service (RADIUS) implementation.
This guide walks through how to set up a RADIUS server on Windows using NPS, from installation to policy configuration.
What Is a Windows RADIUS Server and How Does NPS Fit In?
A RADIUS server authenticates users’ identities and authorizes them for network use. A user becomes authorized for network access after enrolling for a certificate from the public key infrastructure (PKI) or confirming their credentials. Each time the user connects, the RADIUS confirms they have the correct certificate or credentials and prevents any unapproved users from accessing the network.
RADIUS servers are typically implemented through NPS if you’re using Windows. Originally created to enforce network access policies, NPS is frequently used as a RADIUS server.
NPS allows you to authenticate clients using Active Directory (AD) through a wide variety of access points, including the following:
- 1X switches
- Wi-Fi
- Virtual private network (VPN)
- Dial-up
- Router-to-router
While the integration between NPS and AD is more or less manageable, it’s an aging technology that is difficult to integrate into more modern infrastructures. This is especially noteworthy if you’re working in the cloud, a gap Microsoft does not fill with a native RADIUS solution.
Prerequisites for RADIUS Server Windows Setup
Before installing NPS, confirm:
- Windows Server version: 2016, 2019 or 2022 (NPS is available in all three)
- Domain membership: NPS must be installed on a domain-joined machine to read AD user account properties.
- Static IP: Assign a static IP to the server — network devices will reference this IP as the RADIUS server address.
- Admin rights: Local administrator rights are required for role installation.
- Firewall rules: Open UDP ports 1812 (authentication) and 1813 (accounting) inbound from your network devices (APs, switches, VPN concentrators).
How to Set Up a RADIUS Server on Windows: Step-by-Step
This walkthrough will guide you through installing RADIUS server roles in Windows server 2019.
1. Set Up a Security Group
In the Active Directory domain, create a security group. Add all of the users that will authenticate through your new RADIUS.
2. Install the Network Policy and Access Services Role
The Server Manager console contains the Add Roles and Features wizard. That wizard handles the installation and configuration of all of the optional Windows Server features, including NPS. Select the Network Policy and Access Services role.
Open Server Manager → Manage → Add Roles and Features. Select Role-based or feature-based installation. Choose the local server. Check “Network Policy and Access Services” and confirm the “Network Policy Server” sub-role is selected. Complete the wizard and wait for the installation to finish.
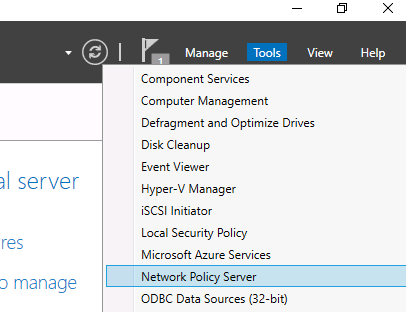
After the role installation is completed, open the Network Policy Server (nps.msc) in the Tools menu.
3. Open the NPS Console
After installation, navigate to Tools → Network Policy Server (or run nps.msc). All remaining configuration happens in this console.

4. Register NPS in Active Directory
In the NPS console, right-click “NPS (Local)” and select “Register server in Active Directory.” Click OK on the confirmation dialog. This step grants NPS permission to read user account dial-in properties from AD — required for user authentication. Without this, authentication requests will fail.
5. Add a RADIUS Client
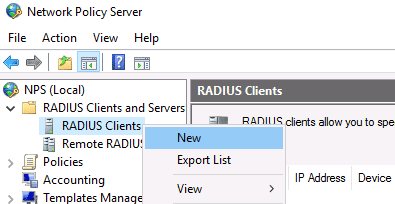
RADIUS clients are the network devices (APs, switches, VPN concentrators) that forward authentication requests to NPS.
To add one, expand RADIUS Clients and Servers → right-click RADIUS Clients → New.
Enter:
- Friendly Name:g., “Office-AP-01”
- Address: IP address or DNS name of the network device
- Shared Secret: A long random string (16+ characters).
This secret must match what is configured on the network device.
Digital certificates offer the best security. Certificates are similarly easy to authorize. Add your access point certificate to the personal certification store on the Local Machine, then request and import the certificate to the NPS server.
SecureW2 allows you to easily generate a custom private CA and export it as a .p12 file for import into NPS. Or, you can import your AD CS certificates and use SecureW2 to enroll end-user devices to self-service themselves for client certificates for your AD CS Certificate Authority (CA).
If you’re using a major access point vendor, navigate to the advanced tab and select the vendor from the “Vendor Name” list. At that point, your Windows Server RADIUS will be ready to go. Users will need to be manually added and removed from the security group unless you use an onboarding solution like the one offered by SecureW2.
6. Create a Connection Request Policy
In the NPS console, select Policies → Connection Request Policies → New. Name the policy (e.g., “Wireless Auth”).
Set conditions for wireless: NAS Port Type = Wireless IEEE 802.11.
Under Settings, confirm “Authenticate requests on this server.” Save the policy.
7. Create a Network Policy
Network policies define what authenticated users can access and how.
Select Policies → Network Policies → New.
Walk through the wizard:
- Policy name: e.g., “RADIUS-WiFi-Users”
- Conditions: Add a Windows Group condition → select the security group created in Step 1 (e.g., “RADIUS-Users”)
- Access granted: Select “Access granted”
- Authentication methods: Add EAP Types. For EAP-TLS: add “Microsoft: Smart Card or other certificate.” For PEAP-MSCHAPv2: add “Microsoft: Protected EAP (PEAP)” and configure with MSCHAPv2 as the inner method.
- Constraints and settings: Configure session timeout, idle timeout and VLAN assignment via Standard RADIUS attributes (Tunnel-Type, Tunnel-Medium-Type, Tunnel-Private-Group-ID) if needed.
8. Set Up a Server Certificate for EAP-TLS (Recommended)
NPS requires a server certificate to negotiate EAP-TLS with clients. The certificate must:
- Be issued by a CA trusted by your client devices
- Include the server’s FQDN as a Subject Alternative Name (SAN)
- Have the TLS web server authentication Extended Key Usage (EKU) value
Options: request a certificate from your internal AD CS CA (auto-enrollment via GPO), import a certificate from a managed PKI like JoinNow Dynamic PKI or use a public CA certificate if your CA is not already trusted by client devices.
For a full guide to RADIUS certificate requirements, see our complete guide to RADIUS servers.
9. Configure Your Network Devices as RADIUS Clients
On each access point, switch or VPN concentrator, configure the RADIUS server settings:
- RADIUS server IP: The static IP of your NPS server
- Authentication port: 1812
- Accounting port: 1813
- Shared secret: The same string entered in Step 6
- Generic navigation: Look for “Security” or “AAA” settings, then “RADIUS server” configuration. The exact menu varies by vendor.
10. Test NPS Authentication
After configuration, test by connecting a device from the security group to the network. Verify in the NPS server’s Windows Event Viewer:
- Event ID 6272: Authentication succeeded
- Event ID 6273: Authentication rejected — includes a Reason Code for troubleshooting
- Command-line verification: netsh nps show eventlog
11. Verify With a Client Device
Connect a managed test device to the configured SSID or switch port. Confirm authentication succeeds and the device receives the correct IP address and VLAN assignment. Check the NPS event log for the corresponding Event ID 6272 to confirm the identity and policy matched.
Common Windows RADIUS Errors and How to Fix Them
Event ID 6273, Reason Code 16: Authentication failed due to a user credentials mismatch. Either the user name provided does not map to an existing user account or the password was incorrect.
The user account is not in the security group defined in the Network Policy conditions, or the account dial-in properties are set to “Deny access.”
To fix: Verify group membership and check the account’s Network Access Permission in ADUC.
Event ID 6273, Reason Code 22: The client could not be authenticated because the EAP type cannot be processed by the server.
This is commonly caused by an expired, misconfigured or untrusted NPS server certificate.
To fix: Push the issuing CA’s root certificate to client devices via Group Policy (Computer Configuration → Windows Settings → Security Settings → Public Key Policies → Trusted Root Certification Authorities).
RADIUS client not responding/timeout
Usually a shared secret mismatch (recheck both sides) or a firewall blocking UDP 1812/1813 between the access point and the NPS server.
To fix: Confirm firewall rules on both the server and any network access control lists (ACLs).
Windows NPS Limitations: Why IT Teams Move to Cloud RADIUS
A major issue with NPS is that using it essentially locks you into using Windows as your vendor. NPS authenticates against Active Directory Domain Services (AD DS). While you can use third-party vendors to overcome this hurdle, it creates unnecessary complications for your infrastructure, putting your network at risk.
Furthermore, Microsoft designed NPS as an on-premises solution with AD, long before cloud solutions became prevalent. There is no native ability to connect NPS with cloud directories. NPS cannot authenticate cloud-only Entra ID users without on-prem AD sync.
NPS does not natively support modern cloud identity providers like Entra ID or Okta, requiring complex directory-sync workarounds that introduce additional failure points.
JoinNow Cloud RADIUS connects cloud identity providers to your existing network infrastructure without on-premises hardware or an expensive forklift upgrade. In addition, Cloud RADIUS and JoinNow Dynamic PKI from SecureW2 integrate with every major AP, MDM and IdP vendor. We’ve worked with countless organizations to migrate to an all-cloud environment using Azure with Cloud RADIUS.
NPS handles basic Windows RADIUS setups, but it becomes a bottleneck as you move toward cloud identity providers and managed devices.
Cloud RADIUS replaces NPS with a fully managed service that supports Entra ID, Okta, Google Workspace and every major MDM out of the box.
Schedule a demo to see how it fits your environment.
Frequently Asked Questions
What is the difference between NPS and a RADIUS server?
NPS (Network Policy Server) is Microsoft’s implementation of a RADIUS server built into Windows Server. RADIUS is the protocol standard — NPS is the Windows-native software that implements it. Other platforms use different RADIUS implementations (FreeRADIUS on Linux, cloud-hosted services), but they all speak the same RADIUS protocol.
Does Windows Server 2022 still support NPS?
Yes, NPS is available in Windows Server 2022 through the Network Policy and Access Services role. However, Microsoft has signaled that NPS will not receive cloud integration improvements, and it does not natively support modern cloud identity providers like Entra ID or Okta without additional configuration workarounds.
What ports does a Windows RADIUS server use?
NPS uses UDP port 1812 for authentication and UDP port 1813 for accounting by default. Make sure these ports are open between your network devices and the NPS server.
What authentication protocols does NPS support?
NPS supports EAP-TLS (certificate-based), PEAP-MSCHAPv2 (password-based), EAP-TTLS and several legacy protocols. EAP-TLS is the most secure option and is recommended for production deployments.